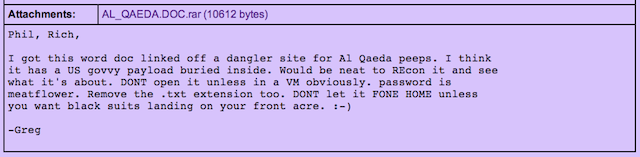
On November 16, 2009, Greg Hoglund, a cofounder of computer security firm HBGary, sent an e-mail to two colleagues. The message came with an attachment, a Microsoft Word file called AL_QAEDA.doc, which had been further compressed and password protected for safety. Its contents were dangerous.
“I got this word doc linked off a dangler site for Al Qaeda peeps,” wrote Hoglund. “I think it has a US govvy payload buried inside. Would be neat to [analyze] it and see what it’s about. DONT open it unless in a [virtual machine] obviously… DONT let it FONE HOME unless you want black suits landing on your front acre. :-)”
The attached document, which is in English, begins: “LESSON SIXTEEN: ASSASSINATIONS USING POISONS AND COLD STEEL (UK/BM-154 TRANSLATION).”
It purports to be an Al-Qaeda document on dispatching one’s enemies with knives (try “the area directly above the genitals”), with ropes (“Choking… there is no other area besides the neck”), with blunt objects (“Top of the stomach, with the end of the stick.”), and with hands (“Poking the fingers into one or both eyes and gouging them.”).
But the poison recipes, for ricin and other assorted horrific bioweapons, are the main draw. One, purposefully made from a specific combination of spoiled food, requires “about two spoonfuls of fresh excrement.” The document praises the effectiveness of the resulting poison: “During the time of the destroyer, Jamal Abdul Nasser, someone who was being severely tortured in prison (he had no connection with Islam), ate some feces after losing sanity from the severity of the torture. A few hours after he ate the feces, he was found dead.”
According to Hoglund, the recipes came with a side dish, a specially crafted piece of malware meant to infect Al-Qaeda computers. Is the US government in the position of deploying the hacker’s darkest tools—rootkits, computer viruses, trojan horses, and the like? Of course it is, and Hoglund was well-positioned to know just how common the practice had become. Indeed, he and his company helped to develop these electronic weapons.
Thanks to a cache of HBGary e-mails leaked by the hacker collective Anonymous, we have at least a small glimpse through a dirty window into the process by which tax dollars enter the military-industrial complex and emerge as malware.
Task B
In 2009, HBGary had partnered with the Advanced Information Systems group of defense contractor General Dynamics to work on a project euphemistically known as “Task B.” The team had a simple mission: slip a piece of stealth software onto a target laptop without the owner’s knowledge.
They focused on ports—a laptop’s interfaces to the world around it—including the familiar USB port, the less-common PCMCIA Type II card slot, the smaller ExpressCard slot, WiFi, and Firewire. No laptop would have all of these, but most recent machines would have at least two.
The HBGary engineering team broke this list down into three categories. First came the “direct access” ports that provided “uninhibited electronic direct memory access.” PCMCIA, ExpressCard, and Firewire all allowed external devices—say a custom piece of hardware delivered by a field operative—to interact directly with the laptop with a minimum amount of fuss. The direct memory access provided by the controllers for these ports mean that devices in them can write directly to the computer’s memory without intervention from the main CPU and with little restriction from the operating system. If you want to overwrite key parts of the operating system to sneak in a bit of your own code, this is the easiest way to go.
The second and third categories, ports that needed “trust relationships” or relied on “buffer overflows,” included USB and wireless networking. These required more work to access, especially if one wanted to do so without alerting a user; Windows in particular is notorious for the number of prompts it throws when USB devices are inserted or removed. A cheerful note about “Searching for device driver for NSA_keylogger_rootkit_tango” had to be avoided.
So HBGary wanted to go the direct access route, characterizing it as the “low hanging fruit” with the lowest risk. General Dynamics wanted HBGary to investigate the USB route as well (the ports are more common, but an attack has to trick the operating system into doing its bidding somehow, commonly through a buffer overflow).
The team had two spy movie scenarios in which its work might be used, scenarios drafted to help the team think through its approach:
1) Man leaves laptop locked while quickly going to the bathroom. A device can then be inserted and then removed without touching the laptop itself except at the target port. (i.e. one can't touch the mouse, keyboard, insert a CD, etc.) 2) Woman shuts down her laptop and goes home. One then can insert a device into the target port and assume she will not see it when she returns the next day. One can then remove the device at a later time after she boots up the machine.
Why would the unnamed client for Task B—which a later e-mail makes clear was for a government agency—want such a tool? Imagine you want access to the computer network used in a foreign government ministry, or in a nuclear lab. Such a facility can be tough to crack over the Internet; indeed, the most secure facilities would have no such external access. And getting an agent inside the facility to work mischief is very risky—if it’s even possible at all.
But say a scientist from the facility uses a memory stick to carry data home at night, and that he plugs the memory stick into his laptop on occasion. You can now get a piece of custom spyware into the facility by putting a copy on the memory stick—if you can first get access to the laptop. So you tail the scientist and follow him from his home one day to a local coffee shop. He steps away to order another drink, to go to the bathroom, or to talk on his cell phone, and the tail walks past his table and sticks an all-but-undetectable bit of hardware in his laptop’s ExpressCard slot. Suddenly, you have a vector that points all the way from a local coffee shop to the interior of a secure government facility.
The software exploit code actually delivered onto the laptop was not HBGary’s concern; it needed only to provide a route through the computer’s front door. But it had some constraints. First, the laptop owner should still be able to use the port so as not to draw attention to the inserted hardware. This is quite obviously tricky, but one could imagine a tiny ExpressCard device that slid down into the slot but could in turn accept another ExpressCard device on its exterior-facing side. This sort of parallel plugging might well go unnoticed by a user with no reason to suspect it.
HBGary’s computer infiltration code then had to avoid the computer’s own electronic defenses. The code should “not be detectable” by virus scanners or operating system port scans, and it should clean up after itself to eliminate all traces of entry.
Greg Hoglund was confident that he could deliver at least two laptop-access techniques in less than a kilobyte of memory each. As the author of books like Exploiting Software: How to Break Code, Rootkits: Subverting the Windows Kernel, and Exploiting Online Games: Cheating Massively Distributed Systems, he knew his way around the deepest recesses of Windows in particular.
Hoglund’s special interest was in all-but-undetectable computer “rootkits,” programs that provide privileged access to a computer’s innermost workings while cloaking themselves even from standard operating system functions. A good rootkit can be almost impossible to remove from a running machine—if you could even find it in the first place.