Dec 9, 2014 | 2020 Relevant, Leaks, Whistleblowers & Dissidents

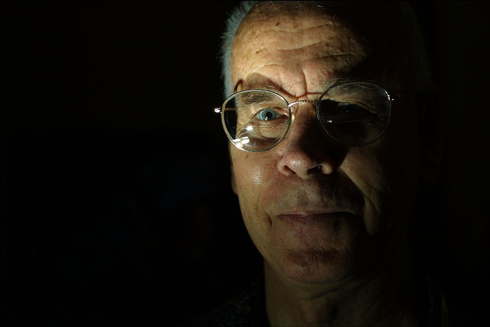
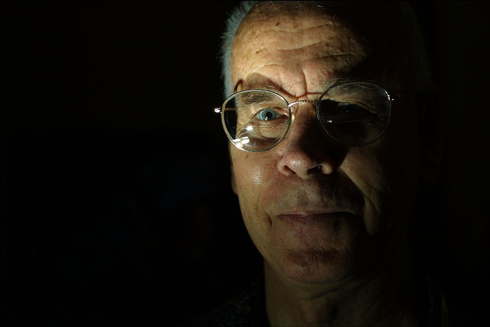
John Young Architect, Cryptologist, Leak Facilitator, Cryptome.org Founder
John Young is a wise, seasoned, and ‘angry’ citizen determined to expose corruption and abhorrent secrecy. He is currently living in New York, doing architectural work for some of the most powerful members of the political establishment that he has sworn to attack. “It’s an easy way to make money in New York, to do corrupt work,” he says with a shrug.
Young on .gov tactics:
“Assassination Politics,” is what Young described as “an imaginative and sophisticated prospective for improving governmental accountability by way of a scheme for anonymous, untraceable political assassination.”
Interesting, Young disclosed the fact on Cryptome in 2000:
“My father-in-law was a longtime career officer in the Central Intelligence Agency, one of its earliest members, and chief of station in several countries…. He’s not talking to Cryptome, and that’s regrettable, for I believe such knowledgeable persons should disclose everything they know about the global culture of secret intelligence and its profound effects – to better inform citizens on the true way their governments function.”
Cryptome.org
Cryptome warns visitors that it does not promise security, that is responsibility of visitors. To not believe security promises by others.
Cryptome Public Key 11 June 2013. New PK for cryptome[at]earthlink.net
Key ID: 0x8B3BF75C
—–BEGIN PGP PUBLIC KEY BLOCK—–
Version: PGP Universal 2.9.1 (Build 347)
mQENBFG3XG8BCACbsuBHhg2txl4ubbd7bia6fND1j6rxt4oXC2NX0gJJ6MJ+Z3BY
nPLCRVX39UsKcXc3NChM4kOF8A650e6nuR3X3pU6UwgwnEUmEi9oSDkAZGDJyKRa
XakSU2jz5PPMdudXWK0GgE9mLWVSn5RchC3RRCDvlbWk4ZKa1N04g/5Hp/iDzmuc
HUeGPMArhnN+1KGIXT5Swh/VJT6zuhMbWncHM0PCTRn5r4lfqfAivP/A2IJNm70/
z6Z6o1rkDVWVN7TXPISi+pEnxbedMtB4aU0RG21v2/kv2Y/ELPTfSjoSkItG7/pK
0LORjgeGR0VIqe3fviWu7rsoFaaExPv3/UYHABEBAAG0IUNyeXB0b21lIDxjcnlw
dG9tZUBlYXJ0aGxpbmsubmV0PokBhwQQAQIAcQUCUbdclTAUgAAAAAAgAAdwcmVm
ZXJyZWQtZW1haWwtZW5jb2RpbmdAcGdwLmNvbXBncG1pbWUHCwkIBwMCCgIZARkY
bGRhcDovL2tleXNlcnZlci5wZ3AuY29tBRsDAAAAAxYCAQUeAQAAAAQVCAkKAAoJ
ELZQVyuLO/dcn20H/08Q+GjrCZI9PhK7CEzJRO3xZxTyI21XMgxTu35fsN/TFM09
ZpgG6IpJfbu+VpW8mBHWyN0lC97IsH4Ep/gV9dix04Rtlokf2QuSnQUfA4WOqsgN
CqVy/fNIYSRoGurqVjIGE+/1eOpahDL4SSeJney9grwqleKxFwWLwnLeAUQoH9xA
8GSrYLW7cL1RJGlfpf0JTKxn3goY8+hcKg1OpM0UjNmeFszJ6iLAUePXTA4P0fpA
JHUuSmZ/NTrxjzlmbbC/O+UVrf+jUxM3pVbehGqGWgxEZsdp0JFTaI02z/+Q1GJY
+gvRDys0dOcumI/PDRWwVkeePYMYC0OigfYwlDKJASIEEAECAAwFAlG3XdoFAwAS
dQAACgkQlxC4m8pXrXyDyQgAknEkbcNKNdhIXlHqF7RliZdtkUdsCByKJqao9Tf/
hhAhcOQVN5DcpxkqMnqiDg6hE4DslE2mA9iRUoqmzjpfk2oRKzk4vntBwTrjPxCM
kPfbW2kPZKj8X7QtXeuMyBKwGvro59s1i+XBQLZD3Qn75OUvwFDAEi459pc9heEB
6wXK293YhyaB92CyDTglPu3Dlv8Qkvgp4cKbdfFCRGwGbQGa8l7jST15NwAmtorr
ydP+IB8rOBku30V31/MFAMrlGhKayhs5vp24b4akQxnrfl4Zdyeoe6Nuq81lr4V6
UN4MZ992Af3Cv0L9bQNgyBKgWswWhSqxlc/gzfeFTPsJybkBDQRRt1xwAQgAywDY
TFabKR1p37QGO0+77Wp0SAtvEMJCpmwKOgxmNtLCoOc9VS+aTkLypE/zpQ8ZGJz4
2gR1vnGrOjwAJLhP/OuNwpqEKmXZ7SklrCEbIFnK0jXWklvc1nKd2XP4UXxGjaHQ
nn2xCzFmDck15a42EBvzdIWr2Xtx8C0cS7i1fXsmdzR8EMfndo/oFMa6lJqu3oil
RYZ/3IFdlnEQlzQxZ2AjoLPW0VbWlwDGqPggvKBPfIk+/cH+pcY3SJJg7RlQwHn5
DRepaCuS3n4kKK5IV5VlNJziYyVsEN2D5BQCtfqHdzkTitRXOgz40tyneX1bqIfI
CRAHhpYYLYIkeEWjPwARAQABiQJBBBgBAgErBQJRt1xxBRsMAAAAwF0gBBkBCAAG
BQJRt1xwAAoJEFaLTmSpng5LAZEH/3N4W4HWdN4NwR04oL/ysFLqHRnRYagA30St
78p/MyZJOMX0372zpoBWBSfXRq8XeSwUXoohugGPyyoIwtINn3/ctZqRziUo6wpF
c7tYIDNd+duA1jMdLjw/rMYcf2LgkFCCN1piAl1014cixpDMM2PXnNbKHDWP91qd
ApdLFnchP/Z4I8gdf4e1itizJ3ONcRT/9iqH3DXCw5CUNckm8ExcBidCC+I4Oh4g
9byDubxQMPzZK54HlK89sUkdvEgQ7QHELNaAP/Y/7IOxAl5AgmIvw/NM4euRL84j
USP8NAIqLbRMMp07kSTVArAMOvmTg7+/rpv9UQkfp1ykBJtr61EACgkQtlBXK4s7
91w4QAf9Gflur6PCr9msaa0mEAi0xcqcmzDkp/Ecms+NKiAjz7U6UT9IgdivFPfi
iyMUTHgOjw5daY/IKaecO0I69wDYRnmLvx9mLjDY+IiQQlw3L9CrN1JLkcUO250p
f3LR/DXFCPgDHdvaTgy0kgg2a4YjKXAirdYyDXGjYgEuM1OvgGLSnDfJ5xJ+Fugq
7IlLoZZQPz/G/k+7c9UDAJ5gaxR9Jyu4aadNsnBD7daO+Mr326fB9M7ded3/gqng
gn/oL6ZkF2QMDWMVcF+qq8CsbqaZMg/UO4obxPbDyCRKE+1ggG+t/tWTMvSoUfEZ
ySZ+3dIlBIbIaHXQCE4ES8wW0JgtaA==
=gjKZ
—–END PGP PUBLIC KEY BLOCK—–
John Young Architect: http://jya.nyc
Special Inspections: http://jya.nyc/special-inspections.htm
Sep 5, 2013 | News

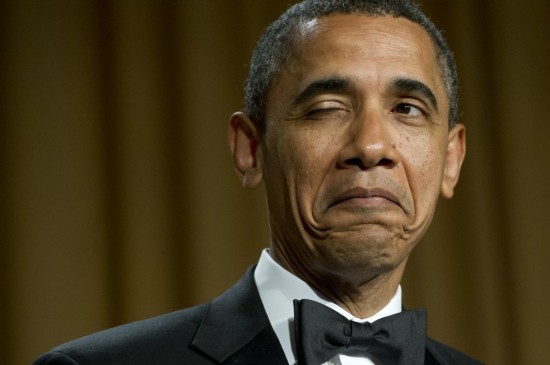
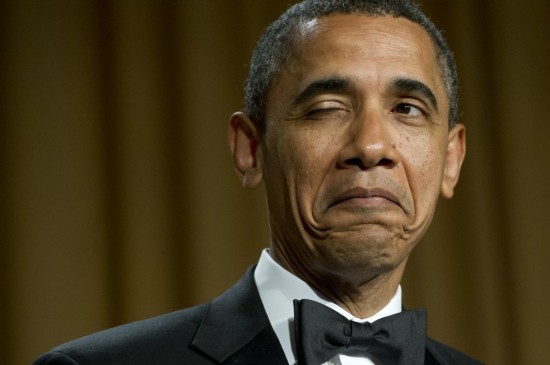
As part of his promises regarding better oversight of the National Security Agency, President Obama called for expert external opinion on where the lines of privacy should be drawn:
Fourth, we’re forming a high-level group of outside experts to review our entire intelligence and communications technologies. We need new thinking for a new era. We now have to unravel terrorist plots by finding a needle in the haystack of global telecommunications. And meanwhile, technology has given governments — including our own — unprecedented capability to monitor communications. – President Obama.
And yet, no. Obama’s panel is not a set of outsiders in the slightest. As some have pointed out in recent days, the group is instead a slurry of insiders, former insiders, and a previous colleague of the president’s.
Member Michael Morell is from the CIA, Richard Clarke is former national security, Cass Sunstein is ex-Obama White House, Peter Swire was part of the Clinton administration, and Geoffrey Stone is also University Chicago stock, same as the president.
Stone, at a minimum, is part of the ACLU, and thus might have a bit of a backbone on the privacy side of things. But the group is surprisingly un-outsidery, and hardly undogmatic. This has not gone unnoticed. However, something that fewer have noticed is that the group contains no technology or telecom folk.
This is almost comical, as we are arguing over digital and telephonic surveillance. PRISM, tapping of fiber-optic cables, storing the nation’s phone records, and forcing telcos to send huge swatches of the Internet to the NSA, and yet not a single voice from the industries impacted will take part.
In the age of cynicism, this must be a high point.
The group is in fact a good mix of people from the establishment who have perspectives on security, but it is utterly incomplete. To exclude from the conversation companies that are directly impacted by the NSA — bullied is probably a better word — is to silence possible dissent. And that is the opposite of open, or fair.
Not that in this discussion there has been much proffered openness of fairness, but when the president assembles a panel of “outsiders” to examine current policy, one could hope for a bit of each. In the assembled group, those in favor of curtailing the NSA’s surveillance activities couldn’t win a voice vote. That’s not so good, really.
If we are going to legally force tech and telco firms to hand over private information of regular folks, they deserve a hand in the discussion. Unless, naturally, the meetings are a sham in the hopes of quieting public outrage and dissent. In that case, a few former insiders can be tossed together for a chat that will mean little and accomplish less. Which appears to be the case.
At each stage of the NSA revelation saga, the government has obfuscuated or offered little. This is another example of the latter.
via TechCrunch
Aug 22, 2013 | DCMX Radio
Bradley Manning To Serve Prison Sentence as Female, Chelsea Manning
(examples of injustice shared on following episode)
Michael Hastings was afraid his car was tampered with!
CLIP: Gun Confiscation Begins In California
NSA files: why the Guardian in London destroyed hard drives of leaked files
NSA Intel Review: Transparent ‘outsiders’ end up being CyberSec ‘insiders’ in more White-house Hypocrisy
LULZ: FBI Says Anonymous no longer effective.. Anonymous responds by Dumping more FBI Databases
Chicken Nuggets..!? Strange Fibers..!? Morgellon’s Disease..!? Human Nuggets..!?
WTF: Swat COP Says America has become a battleground and have same dangers as soldiers in Afghanistan??


Jun 12, 2012 | Anonymous

The State Department and the online mob are both destroying “Internet freedom.”
It’s hard to deny the intellectual ambiguity of “Internet freedom” when among its staunchest defenders are idealistic hacktivists from Anonymous and hard-nosed diplomats from the U.S. State Department—two groups that otherwise disagree on everything else. Ironically, both may end up hurting the very noble cause that they seek to promote.
The diplomats’ problems are quite well-known by now. While Hillary Clinton likes to give speeches in which she fashions herself the world’s greatest defender of “Internet freedom,” the harsh reality is that her own government is its greatest enemy. Given the never-ending flow of draconian copyright and cybersecurity laws coming from Washington, this fact is getting harder and harder to conceal from the global public, who starts to wonder why American diplomats keep criticizing Russia or China but don’t say anything about the impressive online spying operation that the National Security Agency is building inUtah. Nor does the State Department object when America’s allies push for harsh surveillance laws; Britain, with its proposed surveillance legislation, is a case in point. America’s “Internet freedom agenda” is at best toothless and at worst counterproductive. While focusing on (and overselling) the liberating promise of social media in authoritarian regimes, it conceals a number of emerging domestic threats that have nothing to do with dictators—and everything to do with aggressive surveillance, disappearing privacy, and the astonishing greed of Silicon Valley.
The case of Anonymous is not as straightforward. This movement is so distributed, fluid, and occasionally disorganized that anyone seeking to pigeonhole it into a coherent ideological doctrine would not get too far. Still, most of its recent high-profile attacks—upon the intelligence firm Stratfor, the Central Intelligence Agency, the signatories of the Anti-Counterfeiting Trade Agreement (which, among other things, aims to thwart Internet piracy), and the Chinese government—are motivated by a desire to defend “Internet freedom.” In this lofty goal, the agendas, if not the approaches, of Anonymous and the State Department overlap.
Why these particular targets? Predictably, Anonymous hates Western governments for ushering in more surveillance and draconian piracy laws; the security industry—for satisfying the growing policing demands of those governments; the Chinese government—for being the world’s mightiest Internet censor.
Such flashy attacks are still widely discussed in the media, and that can inspire valuable broader discussion of some important Internet issues, such as the controversial Cyber Intelligence Sharing and Protection Act. But spectacles, which are bound to get boring, are not a sustainable political strategy, as the media will eventually lose interest. And Anonymous has yet to go beyond spectacle and offer a more meaningful way for its members to contribute. Cyberattacks are cheap, easy, and can attract thousands of participants without demanding much of them. In this, they can be seen as a form of “slacktivism”—they make everyone feel good but don’t necessarily advance the cause. They can be great for stunts, but one can’t change the world with stunts alone.
But—yet another parallel to the State Department—it’s not just that Anonymous’ campaigns might be toothless. They may prove counterproductive as well. The cybersecurity industry has almost certainly benefited from the buzz and fear-mongering generated by Anonymous’ attacks. Every new incursion by Anonymous must be greeted as good news in the offices of companies providing cyberdefense to both public and private sectors. Now that Anonymous has revealed that even private intelligence-gathering firms are not safe—a few months ago, it obtained the emails from Stratfor, which eventually were published by WikiLeaks—it’s a great time to be a provider of cybersecurity services!
The hacktivists keep supplying the industry with strong examples as to why more public money should be spent beefing up Internet security and surveillance while eliminating online anonymity. Take Anonymous’ recent assaults on the websites of USTelecom and Tech America, two leading technology trade associations that have lent their support to CISPA. It doesn’t take a genius to realize that a cyberattack against groups that promote legislation to combat cyberattacks only strengthens their case. It’s like shooting a bazooka in a legislative session about gun control. This was not lost on those trade associations, and they exploited this gift from Anonymous to its fullest. Thus, the president of USTelecom
claimed that “by their actions Anonymous hacktivists underscore the importance of speedy action on the bipartisan [CISPA] legislation to ensure that the Internet remains an open and safe forum for all.” Regardless of what happens to this particular piece of legislation, it’s likely that lawmakers will be under growing pressure from the
military-digital complex to do something about Anonymous’ attacks—and that “something” would not be conducive to any kind of “Internet freedom.”
We can expect similar developments to take place in China, where in early April a group that calls itself “Anonymous China” defaced several government websites and promised to take down its notorious censorship system. The damage caused is minimal, while the symbolic value derived from exposing the Chinese Internet censorship to the international audiences is arguably insignificant. It’s already a well-known problem. But Anonymous’ attacks do give the Chinese government good reasons to invest money into online surveillance and, perhaps, even do it with popular support: Anonymous is not above exposing credit card details of innocent victims—and China’s burgeoning middle classes will easily grasp the implications of online insecurity. If the strikes continue, Anonymous may be China’s equivalent of Stuxnet—the computer worm that disrupted Iranian nuclear facilities—only without imposing any of Stuxnet’s crippling costs. Iran’s ongoing flirtation with the idea of a “national Internet,” itself a reaction in part to Stuxnet, is a good example of how the rhetoric of cyberattacks may be invoked to justify more Internet control.
Why doesn’t Anonymous seek more effective means of cyberactivism? This is where the organization’s decentralized structure is a liability, not an asset. The movement that claims to have no leaders—well, aside from those “leaders” who happen to be working for the FBI—and that means short-term, easy objectives (often bordering on pranks) can take precedence over long-term strategic goals.
The very idea of an online campaign to defend “Internet freedom” is problematic. It’s not like an appeal to raise money for a presidential candidate or victims of a natural disaster; it takes more than a few clicks or cash donations. Moreover, the goals and priorities of such a campaign are likely to shift all the time, depending on the political context. Defending “Internet freedom” requires constant interpretation, deliberation, and discrimination between different courses of action. In contrast, online fundraising usually has fixed goals and is amenable to small-scale, granular contributions.
Without greater bureaucratization, formal mechanisms for decision-making, and, more importantly, the capacity to accept responsibility when those decisions bring unfortunate consequences, Anonymous may end up posing as great of a threat to Internet freedom as its main nemesis, the U.S. government.
Source: http://www.slate.com/articles/technology/future_tense/2012/04/internet_freedom_threat_posed_by_hillary_clinton_s_state_department_and_anonymous_.single.html