What Are IMSI Catchers and How Do They Work
If you have ever noticed your cell phone signal degrading suddenly at a large public gathering, there may be a technological explanation beyond simple network congestion. Devices known as IMSI catchers, portable surveillance tools already on the market and actively marketed to law enforcement and intelligence agencies, can intercept mobile communications in ways that are virtually undetectable to phone users.
IMSI stands for International Mobile Subscriber Identity. An IMSI catcher functions as a rogue cell tower, mimicking legitimate cellular infrastructure to trick nearby phones into connecting to it instead of an actual tower. This type of interception is classified as a man-in-the-middle attack. Once a phone connects, the device can force it to drop its encryption, enabling the operator to intercept calls, text messages, and data transmissions. In some configurations, the operator can also manipulate outgoing messages.

Wearable Surveillance at Public Gatherings
In mid-2012, electronic privacy advocate Chris Soghoian presented research at TED in Scotland that included a photograph taken by Privacy International researcher Eric King at a surveillance industry trade show. The image showed an IMSI catcher small enough to be strapped to a person’s body and concealed beneath a shirt.
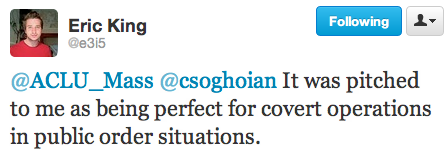
According to King, the device was marketed to him as being ideal for covert operations in public order situations, a phrase that translates directly to deployment at protests and demonstrations. The miniaturization of this technology meant that surveillance operators could move through crowds while passively collecting mobile data from everyone in range.
Law Enforcement Use Without Warrants
The FBI acknowledged using IMSI catchers, marketed under brand names like Stingray, while maintaining that no warrant was required for their deployment. This legal position was being challenged in court proceedings that had not yet been resolved at the time these concerns emerged.
The Electronic Privacy Information Center (EPIC) filed Freedom of Information Act litigation seeking details about how the FBI used Stingray devices, including the legal standards applied before deployment. The bureau resisted disclosure, leaving significant questions unanswered about the scope and frequency of domestic IMSI catcher use.
U.S. law enforcement agencies more broadly claimed that tracking a phone’s location through electronic spoofing did not require a warrant, a position that put them at odds with privacy advocates who argued that such intrusive surveillance should require judicial authorization.
Vulnerabilities That Affect Everyone
The security implications of IMSI catcher technology extended well beyond government surveillance. As privacy researchers noted in court filings, the same vulnerabilities in cellular networks that allowed law enforcement to intercept communications could be exploited by criminals, stalkers, and foreign intelligence services conducting espionage.
At the 2011 DefCon security conference, researcher Chris Paget demonstrated the practical reality of cellphone spoofing by intercepting signals from audience members’ phones during his presentation, illustrating how accessible the technology had become.
The fundamental problem was that mobile phone networks contained architectural weaknesses that IMSI catchers exploited. Individual users had essentially no way to detect or defend against these devices. The encryption that phones use to protect communications could be forcibly downgraded or disabled entirely by a well-equipped interceptor.
Technology Outpacing Legal Protections
The proliferation of IMSI catchers highlighted a persistent gap between surveillance technology capabilities and the legal frameworks designed to protect privacy. Existing wiretapping laws were written for an era of landline telephones and did not adequately address portable interception devices that could sweep up communications from hundreds of phones simultaneously.
Privacy advocates called for congressional action to update electronic surveillance laws, arguing that the public interest required both stronger legal protections and greater transparency about how these technologies were being used. The tension between security operations and civil liberties at public gatherings remained unresolved, with the technology continuing to advance faster than the law could adapt.

