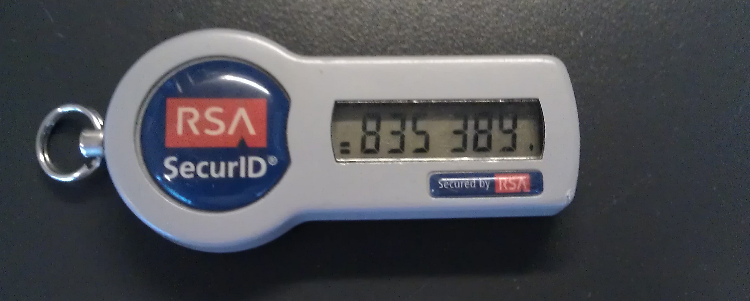
RSA was hacked in March. This was one of the biggest hacks in history.
The current theory is that a nation-state wanted to break into Lockheed-Martin and Northrop-Grumman to steal military secrets. They couldn’t do it, since these companies were using RSA SecurID tokens for network authentication. So, the hackers broke into RSA with a targeted e-mail attack. They planted a backdoor and eventually were able to gain access to SecurID information that enabled them to go back to their original targets and successfully break in. In the aftermath of the attack, RSA was forced to replace SecurID tokens for their customers around the world.
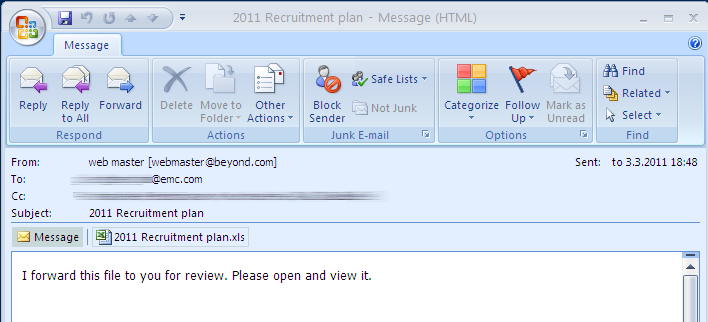
Already in April, we knew that the attack was launched with a targeted e-mail to EMC employees (EMC owns RSA), and that the e-mail contained an attachment called “2011 Recruitment plan.xls“. RSA disclosed this information in their blog post. Problem was, we didn’t have the file. It seemed like nobody did, and the antivirus researcher mailing lists were buzzing with discussion about where to find the file. Nobody had it, and eventually the discussion quieted down.
This bothered Timo Hirvonen. Timo is an analyst in our labs and he was convinced that he could find this file. Every few weeks since April, Timo would go back to our collections of tens of millions of malware samples and try to mine it to find this one file — with no luck. Until this week.
Timo wrote a data analysis tool that analyzed samples for flash objects. We knew the XLS file in question used a Flash object to take over the system. The new tool located several relevant samples. However, one of them was not an Excel file. It was an Outlook message file (MSG). When Timo opened it up, he knew he was onto something. The message file turned out to be the original e-mail that was sent to RSA on the 3rd of March, complete with the attachment 2011 Recruitment plan.xls.
After five months, we finally had the file.
And not only that, we had the original e-mail. Turns out somebody (most likely an EMC/RSA employee) had uploaded the e-mail and attachment to the Virustotal online scanning service on 19th of March. And, as stated in the Virustotal terms, the uploaded files will be shared to relevant parties in the anti-malware and security industry. So, we all had the file already. We just didn’t know we did, and we couldn’t find it amongst the millions of other samples.
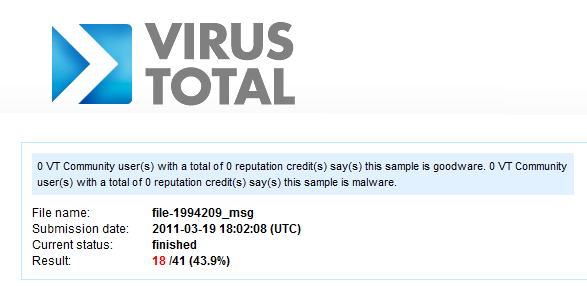
The sample was uploaded on 19th of March as file-1994209_msg
So, what did the e-mail look like? It was an e-mail that was spoofed to look like it was coming from recruiting website Beyond.com. It had the subject “2011 Recruitment plan” and one line of content:
“I forward this file to you for review. Please open and view it“.
The message was sent to one EMC employee and cc’d to three others.
When opened, this is what the XLS attachment looked like:
Here’s a YouTube video that shows in practice what happens when you open the malicious Excel file.
In this video you can see us opening the e-mail to Outlook and launching the attachment. The embedded flash object shows up as a [X] symbol in the spreadsheet. The Flash object is executed by Excel (why the heck does Excel support embedded Flash is a great question). The Flash object then uses the CVE-2011-0609 vulnerability to execute code and to drop a Poison Ivy backdoor to the system. The exploit code then closes Excel and the infection is over.
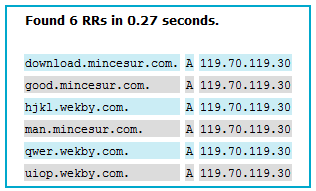
After this, Poison Ivy connects back to its server at good.mincesur.com. The domain mincesur.com has been used in similar espionage attacks over an extended period of time.
Once the connection is made, the attacker has full remote access to the infected workstation. Even worse, it has full access to network drives that the user can access. Apparently the attackers were able to leverage this vector further until they gained access to the critical SecurID data they were looking for.
The attack e-mail does not look too complicated. In fact, it’s very simple. However, the exploit inside Excel was a zero-day at the time and RSA could not have protected against it by patching their systems.
So, was this an Advanced attack? The e-mail wasn’t advanced. The backdoor they dropped wasn’t advanced. But he exploit was advanced. And the ultimate target of the attacker was advanced. If somebody hacks a security vendor just to gain access to their customers systems, we’d say the attack is advanced, even if some of the interim steps weren’t very complicated.
Timo will be discussing his research on the topic in detail in the T2 Data Security conference in October in his talk titled
“How RSA Was Breached“.
P.S. For those who are still looking for the sample:
MD5 of the MSG file: 1e9777dc70a8c6674342f1796f5f1c49
MD5 of the XLS file: 4031049fe402e8ba587583c08a25221a