
TrapWire Surveillance System Sparks Growing Controversy
What happens when an obscure intelligence firm gets caught running one of the most sweeping domestic monitoring programs ever uncovered? If you are Cubic Corporation, the answer involves a cascade of increasingly damaging revelations that extend far beyond the original TrapWire exposé.
Within days of the initial reporting by RT that revealed TrapWire — a sprawling, technologically sophisticated surveillance apparatus — independent researchers began pulling on threads that connected the program to a web of corporate entities, government contracts, and covert operations targeting American political activists.
Ntrepid’s Tartan Platform: Mapping Protest Networks With FBI Help
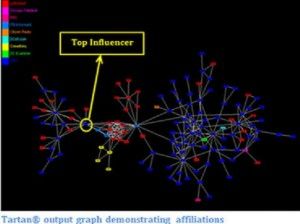
Among the most alarming discoveries was a product called Tartan, developed by the Ntrepid Corporation. According to its own promotional materials, Tartan claimed to uncover hidden relationships within social networks using mathematical modeling and algorithmic analysis. The company’s website featured a case study from 2012 that specifically examined connections among individuals the firm labeled as anarchists — a category that, remarkably, encompassed Occupy Wall Street organizers, PBS, Citizen Radio, and Crimethinc.
The Tartan promotional documents painted these disparate groups as components of a shadowy network employing influential organizers, digital communication tools, and what the company characterized as unlawful strategies to propagate disorder across the United States. Most troubling, the accompanying network diagram included an unnamed FBI informant among the mapped nodes, raising serious questions about federal involvement in monitoring constitutionally protected political expression.
Ntrepid’s Track Record: Military Propaganda and Fake Online Personas
Ntrepid had already drawn scrutiny in 2011 when The Guardian revealed the company was managing an “online persona management” operation — essentially a government-funded propaganda machine. The U.S. Central Command had awarded Ntrepid a $2.76 million contract to generate fabricated internet identities, commonly referred to as sock puppet accounts, designed to shape public opinion in support of American strategic objectives abroad, according to documents from the Defense Department’s Inspector General.
The Corporate Paper Trail Linking Ntrepid, Abraxas, and TrapWire
Investigations conducted by journalists, the transparency project known as Project PM (led by Barrett Brown), the civil liberties organization PrivacySOS, and independent researchers Justin Ferguson and Asher Wolf uncovered a paper trail connecting Tartan’s parent company directly to TrapWire through shared corporate leadership.
Margaret A. Lee of Northern Virginia appeared in public filings as secretary on the Ntrepid board, alongside Director Richard Helms (a former CIA officer who once oversaw the agency’s European division), Chief Financial Officer Wesley R. Husted, and President Michael Martinka. Virginia State Corporation Commission records showed that TrapWire Inc. was registered to Lee on March 7, 2009. Additional documents confirmed that Husted had served as CFO of TrapWire Inc., while Helms held the position of CEO.
Researcher Justin Ferguson documented that Lee, Helms, and Husted all appeared on Abraxas Dauntless filings with Virginia as recently as December 2011, on TrapWire filings from September 2011, and on Ntrepid’s most current annual report with the Florida Division of Corporations.
Cubic Corporation’s Denials Contradict Public Records
Despite this documented overlap in leadership, Cubic Corporation aggressively denied any connection. In an August 2010 press release, the company stated that Abraxas Corporation had no affiliation whatsoever with Abraxas Applications, the entity that became TrapWire Inc.
However, a 2007 Washington Business Journal article described the two Abraxas entities as essentially the same organization, noting that a software division had been separated from the parent company specifically to market the TrapWire product. A 2006 article from the same publication documented that Abraxas had acquired the software firm Dauntless — and researchers at Darkernet subsequently confirmed that Lee, Husted, and Helms all served on the Abraxas Dauntless board of directors as well.
Barrett Brown reported obtaining Cubic’s 2010 tax filings, which showed Ntrepid was wholly owned by Cubic — mirroring the same ownership structure as Abraxas. Meanwhile, publicly available trademark records indicated that Abraxas Corporation first filed to register the TrapWire name in 2004 and received formal trademark approval in January 2007.
When confronted with these findings, Cubic communications director Tim Hall continued to insist in recorded conversations that no link existed between Abraxas Applications, TrapWire, and Ntrepid.
How TrapWire Works: Global Surveillance at Unprecedented Scale
The scope of TrapWire itself proved staggering. According to details extracted from the Stratfor email archive published by WikiLeaks, the system represented one of the most technologically advanced civilian surveillance platforms ever constructed. Former intelligence officials designed it to continuously capture data at monitoring points across major American cities and landmarks, encrypting and transmitting it in real time to a secure central database for aggregation with other intelligence feeds.
Transparency organization Public Intelligence reported that Stratfor emails indicated TrapWire was deployed by the U.S. Secret Service, British intelligence service MI5, the Royal Canadian Mounted Police, counterterrorism units within the Los Angeles and New York City police departments, the LA fusion center, and multiple military installations. A July 2011 internal Stratfor email described the Army, Marine Corps, and Pentagon as already integrated into the system, with the Navy identified as the next branch to come online.
Training Programs Reveal Predictive Policing Philosophy
An investigation published by the online outlet Darkernet shed additional light on TrapWire’s operational philosophy through its training curriculum. The Surveillance Awareness Workshop taught operators to evaluate facilities through the lens of a potential attacker and to recognize what the company termed “indicators of pre-attack surveillance” — a framework that effectively presumed guilt based on behavioral patterns rather than evidence of criminal activity.
A second course, the Terrorist Pre-Attack Operations Course, similarly trained participants to identify behavioral signatures supposedly associated with imminent criminal or terrorist action. Critics noted that neither the technology nor its training materials offered clear definitions of who qualified as a “terrorist” or “criminal,” leaving those determinations to the subjective judgment of individual operators.
The third documented training module, called Deception Detection and Eliciting Responses, taught interrogation techniques for use on individuals flagged by TrapWire’s automated behavioral analysis. The combination of mass algorithmic surveillance with subjective interrogation methods raised fundamental constitutional concerns about presumption of innocence and protection against unreasonable searches.
Broader Implications for Civil Liberties
The convergence of TrapWire’s surveillance infrastructure with Cubic Corporation’s existing access to personal data through its other business lines — including fare card systems for major public transit networks and online identity management tools like Anonymizer, which Cubic acquired in 2010 — amplified concerns about the potential for abuse. The integration of surveillance cameras, facial recognition technology, social network mapping, and behavioral profiling into a single corporate ecosystem represented a qualitative leap in the capacity to monitor ordinary citizens engaged in lawful activity.
The persistent efforts by WikiLeaks to publish these revelations were met with sustained distributed denial-of-service attacks against the organization’s servers, which some outlets attributed to actors within the American intelligence community seeking to suppress coverage of the story.
This article is based on reporting originally published by RT, The New American, and Darkernet. All factual claims are attributed to the sources cited.



