Bitcoin’s Anonymity Problem
Bitcoin is frequently described as an anonymous digital currency, but this characterization is misleading. While it may be possible to conduct transactions in ways that obscure identity, the public nature of the blockchain means that many users and their transactions can be traced through careful analysis. Research published on arXiv in 2011 demonstrated just how vulnerable Bitcoin users are to de-anonymization through passive network analysis of publicly available data.
How Network Analysis Exposes Bitcoin Users
The core finding of the research was that anonymity is not a prominent design goal of Bitcoin. Using tools from network analysis and publicly available blockchain data, researchers were able to map relationships between users, trace the flow of funds, and in many cases identify individuals behind supposedly anonymous transactions.
The methodology involved constructing user networks where each vertex represents a user and each directed edge represents a flow of Bitcoins between public keys belonging to different users. By examining egocentric networks — the connections radiating outward from a specific user — patterns emerged that linked seemingly unrelated transactions to the same individuals.
Centralized services such as exchanges, mixers, and wallet providers were identified as having access to even more detailed information. An active analysis using marked Bitcoins and collaborating participants could reveal additional details beyond what passive observation alone could uncover.
Case Study: Tracing a 25,000 Bitcoin Theft
To illustrate these findings, the researchers examined a notable case involving the theft of 25,000 Bitcoins. The victim reported waking on the morning of June 13, 2011, to discover a large portion of his holdings had been transferred to an unfamiliar address. The theft occurred at 16:52:23 UTC, shortly after someone compromised the victim’s Slush mining pool account and changed the payout address.
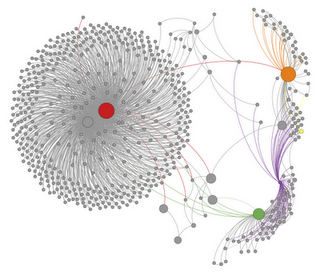
The egocentric network visualization above shows the thief’s connections within the Bitcoin user network. The red vertex represents the thief and the green vertex represents the victim. Each directed edge is colored by its source vertex, and the network reveals that the victim and thief were connected by paths beyond just the theft transaction itself.
Uncovering Hidden Connections
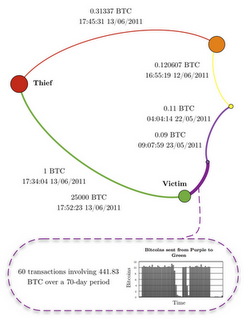
A sub-network analysis revealed a cycle connecting the thief, the victim, and three other notable entities. Using off-network data, researchers identified that one vertex corresponded to the main Slush mining pool account, while another was linked to the hacker group LulzSec.
Key observations from this sub-network included:
- The large 25,000 BTC theft was preceded by a smaller test theft of just 1 BTC
- The thief sent 0.31337 BTC (a nod to “eleet” hacker culture) to LulzSec shortly after the theft
- A fourth user in the network was identified as both a Slush pool member and a one-time LulzSec donator, whose last known activity using those public keys occurred one day before the theft
While at least one attempt was made to publicly associate the thief with LulzSec, the researchers noted this particular claim was fabricated after the theft.
Following the Money Through Flow Analysis
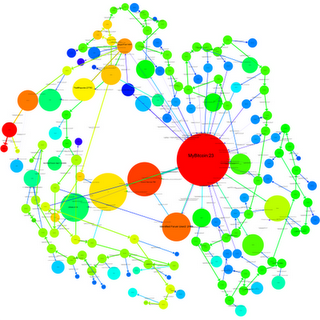
Beyond static network mapping, the researchers built tools to trace significant flows of value over time. When a user received a large volume of Bitcoins relative to their estimated balance and then quickly transferred a significant proportion onward, this was flagged as noteworthy.

The analysis identified four significant outflows from the stolen funds beginning at 19:49, 20:01, 20:13, and 20:55 UTC on the day of the theft. Two of these flows were particularly revealing:
The flow that began at 20:55 split at a specific vertex, with some Bitcoins rejoining the flow from 20:13. This merging pattern, combined with subsequent transfers, allowed researchers to determine that four previously unseen public keys — receiving Bitcoins from two flows that had split apart two days earlier — all belonged to the same user.
Another notable flow involved movement through thirty unique public keys in rapid succession, with small amounts of approximately 30 BTC (worth roughly $500 at the time) siphoned off at each step. On June 20, 2011, each of these smaller holdings was transferred to a public key operated by the MyBitcoin service — a key that had been previously involved in a separate, unrelated Bitcoin theft.
WikiLeaks Donations and the Illusion of Anonymity
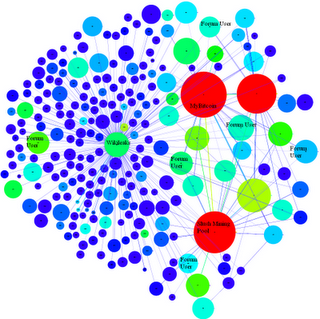
The research also examined WikiLeaks’ public Bitcoin donation address, which was promoted on Twitter with the claim that “Bitcoins cannot be easily tracked back to you.” While WikiLeaks did describe a more secure donation method involving one-time public keys, those who donated directly to the published address were far more exposed than they likely realized.
Using information gathered from Bitcoin forums, the Bitcoin Faucet, and Twitter, researchers were able to resolve several users in the WikiLeaks egocentric network with identifying information. These users could be linked either directly or indirectly to their donations, undermining the assumption of anonymity.
Implications for Cryptocurrency Privacy
This early research demonstrated that straightforward passive analysis of public blockchain data could de-anonymize considerable portions of the Bitcoin network. The techniques employed — egocentric network visualization, flow tracing, community finding, block modeling, and network flow algorithms — required no special access or cooperation from service providers.
The findings carried an important message for the cryptocurrency community: users should not operate under a false expectation of anonymity when using Bitcoin. The public ledger that makes Bitcoin trustless and decentralized also makes it inherently traceable, and the gap between perceived and actual privacy remains a fundamental tension in cryptocurrency design to this day.



