Privacy advocates urged everyday internet users to adopt email encryption after a previously unseen tutorial video created by Edward Snowden became publicly available in May 2014. The former NSA contractor produced the 12-minute clip to teach journalists how to communicate with him securely — and its release reignited debate over whether ordinary citizens should protect their digital correspondence from government surveillance.
Why Snowden Created the Encryption Video
Snowden recorded the tutorial specifically for Glenn Greenwald, then a reporter at The Guardian, as a step-by-step guide to establishing secure communications. The goal was straightforward: enable Greenwald to receive leaked documents through channels that intelligence agencies could not intercept. Snowden disguised his voice using software throughout the recording to avoid identification by NSA or GCHQ analysts.
The video surfaced publicly to coincide with the release of Greenwald’s book No Place to Hide, which chronicled the story behind what many consider the most consequential intelligence leak in American history.
How Public Key Encryption Works According to Snowden
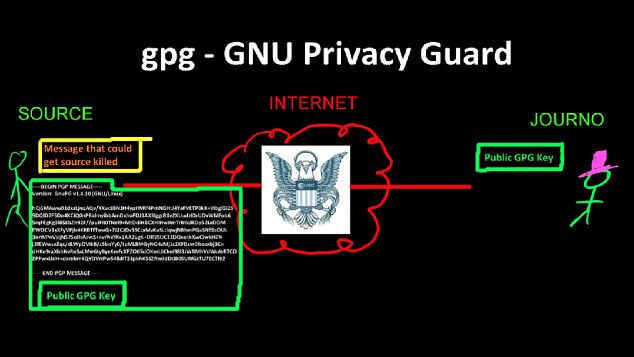
In the video, Snowden explained that conventional emails travel across the internet as unencrypted plain text, making them readable by anyone who intercepts them along the way. Any router between sender and recipient could be monitored by an intelligence service or a random hacker. Email providers like Gmail could also be compelled to hand over stored messages through subpoenas or other legal mechanisms — or even through illegal means.
The solution, Snowden argued, was Public Key Encryption (PKE). He acknowledged that traditional encryption methods require both parties to share a secret password — but transmitting that password over the same compromised channels defeats the purpose entirely. He used a memorable example: sending an encrypted file with the note that the password is “cheesecake” means the entire internet now knows the password is “cheesecake.”
PKE solves this problem through an elegant mathematical approach. A journalist publishes a public key that anyone can access. Sources use that key to encrypt messages that only the journalist’s corresponding private key can unlock. The system’s design means that possessing the public key provides zero advantage to an eavesdropper.
Snowden’s Step-by-Step GPG4Win Tutorial
The tutorial walked viewers through installing and using GPG4Win, a free program that implements Public Key Encryption, then demonstrated how to transmit encrypted messages over the Tor anonymity network. The video’s description on Vimeo promised that following the instructions would allow any potential source anywhere in the world to send a powerfully encrypted message that only the intended recipient could read — even if the two parties had never previously met or exchanged contact information.
Even Greenwald found the tutorial challenging. The journalist admitted he was unable to finish the video on his first attempt. It took him seven weeks and assistance from technical experts before he could establish secure communications with Snowden.
Why Mass Encryption Adoption Remained Difficult
The video’s publication arrived as growing numbers of internet users were experimenting with encryption tools, motivated by alarm over Snowden’s revelations. His leaked documents had exposed that the NSA and Britain’s GCHQ possessed the capability to monitor virtually anyone’s communications, track social media activity in real time, and log the locations of billions of mobile devices worldwide. Public anger intensified when it emerged that these tools were being deployed against American citizens without warrants and used to tap the phones of allied world leaders — directly contradicting assurances the NSA had given to Congress.
Javier Ruiz, director of policy at the Open Rights Group, compared unencrypted emails to postcards and encryption to tamper-proof envelopes. He noted that professionals handling confidential information — journalists, legislators, doctors, lawyers — should always encrypt their communications. But he emphasized that achieving widespread adoption would require major technology companies like Google, Apple, and Microsoft to build encryption directly into their products.
TK Keanini, chief technology officer at internet security firm Lancope, expressed skepticism that this would happen. He described PGP and similar tools as simply too complicated for average users — managing key pairs, understanding certificate revocation, and navigating related technical concepts had limited adoption to highly technical users over the preceding two decades. While a service like Gmail could theoretically integrate user-friendly encryption, Keanini argued it would never happen because free email providers generate revenue precisely because user data remains unencrypted and available for advertising purposes.
The Tension Between Technology and Policy Solutions
Mike Rispoli of Privacy International argued that technological self-defense, while essential, should not be the only answer. He stressed that citizens should never be forced to take extraordinary measures simply to exercise their fundamental rights. The real solution required political, legal, and technological approaches working in concert to ensure privacy protections were upheld. While individuals could use encryption to empower themselves, the broader fight demanded challenging government policies and intelligence agency practices that enabled mass surveillance of populations worldwide.
Originally published May 15, 2014. Content adapted from reporting on Snowden’s encryption tutorial release.