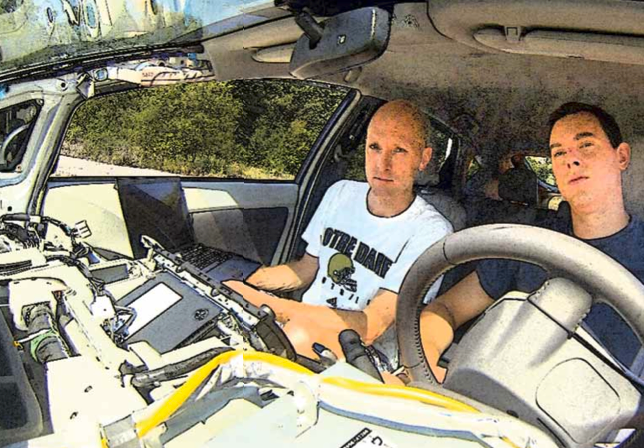
Hackers Chris Valasek and Charlie Miller have demonstrated from the backseat of a Toyota Prius that all you need is a Macbook and a USB cable in order to hack into a computer-controlled car.
Valasek is the director of security intelligence for IOActive and Miller is a security engineer for Twitter.
These two security researchers showed that they can turn off the breaks, for example, even if the driver is at the helm.
Using a grant from the Defense Advanced Research Projects Agency (DARPA), Miller and Valasek have been researching computerized car vulnerabilities since 2012 and will be displaying their findings at DEF CON, a hacker’s conference in Las Vegas next month.
Miller asserted that they “had full control of braking” and that they “disengaged the brakes so if you were going slow and tried to press the brakes they wouldn’t work. We could turn the headlamps on and off, honk the horn. We had control of many aspects of the automobile.”
• Turn off power to the steering
• Have the onboard GPS give incorrect directions
• Change the numbers on the speedometer
• Force the car to change direction
Miller explained: “At the moment there are people who are in the know, there are nay-sayers who don’t believe it’s important, and there are others saying it’s common knowledge but right now there’s not much data out there. We would love for everyone to start having a discussion about this, and for manufacturers to listen and improve the security of cars.”
Using the vehicle’s electronic control unit (ECU) and the on-board diagnostics port (OBD), Miller and Valasek gained control over a 2010 Ford Escape and Toyota Prius.
ECUs are embedded systems that “controls one or more of the electrical system or subsystems in a motor vehicle.”
The OBD is the “vehicle’s self-diagnostic and reporting” apparatus that “gives the vehicle owner or repair technician access to the status of the various vehicle sub-systems.”
A representative from Toyota explained that the hacker would have to be in the car to manipulate its systems.
He said: “Altered control can only be made when the device is connected. After it is disconnected the car functions normally. We don’t consider that to be ‘hacking’ in the sense of creating unexpected behavior, because the device must be connected – ie the control system of the car physically altered. The presence of a laptop or other device connected to the OBD [on board diagnostics] II port would be apparent.”
Hacking into cars that are remotely controlled, such as Google’s self-driving vehicles, is a concern and this researcher could uncover implications for security purposes.
In 2010, teams from the University of Washington (UW) and the University of California (UC) were able to breach the computer systems of cars using cellular phone connections, Bluetooth headsets and a CD.
Stefan Savage from UC explained that their research “explores how hard it is to compromise a car’s computers without having any direct physical access to the car.”
Computerized cars “contain cellular connections and Bluetooth wireless technology” that could be tapped into remotely and used to take over the controls of the vehicle, listen into the conversations taking place in the cab of the car and completely compromise the safety of the vehicle.
Because computer connections to cars are virtually indistinguishable from internet-connected computers, their propensity toward vulnerabilities from outside influences are similar.
Using an On-Star navigation unit, a hacker could utilize the controls a remote technician at the GPS corporation’s on-call center because they are fully capable of controlling a vehicle in the event of an accident or call from a customer.
With complete disregard for driver privacy, the Obama administration gave their consent to the National Highway Traffic Safety Administration (NHTSA) to mandate black box event data recorders (EDR) be installed in all new cars in the US.
The NHTSA says that by September 2014 all car and light trucks will be equipped with EDRs that will silently “record the actions of drivers and the responses of their vehicles in a continuous information loop.”
The information recorded by EDRs includes:
• vehicle speed
• whether the brake was activated in the moments before a crash
• crash forces at the moment of impact
• information about the state of the engine throttle
• air bag deployment timing and air bag readiness prior to the crash
• whether the vehicle occupant’s seat belt was buckled
The NHTSA claims that “EDRs do not collect any personal identifying information or record conversations and do not run continuously.”
Advanced EDRs can collect detailed information about drivers and their driving habits; including the size and weight of the driver, the seat position, the habits of the driver as well as passengers.
The excuse is the EDRs gather information about car crashes in the moments leading up to the accident that manufacturers can use to improve their safety measures when constructing vehicles. However, the government regulation utilizes surveillance technology with policies that do not outline the expressed use of the data collected in the EDRs.