In 2008, a Reston, VA based corporation called Oceans’ Edge, Inc. applied for a patent. On March, 2012 the company’s application for an advanced mobile snooping technology suite was approved.
The patent describes a Trojan-like program that can be secretly installed on mobile phones, allowing the attacker to monitor and record all communications incoming and outgoing, as well as manipulate the phone itself. Oceans’ Edge says that the tool is particularly useful because it allows law enforcement and corporations to work around mobile phone providers when they want to surveil someone’s phone and data activity. Instead of asking AT&T for a tap, in other words, the tool embeds itself inside your phone, turning your device against you.
A former employee of Oceans’ Edge notes on his LinkedIn page that the company’s clients included the FBI, Drug Enforcement Agency, and other law enforcement.
Oddly enough, Oceans’ Edge, Inc. describes itself as an information security company on its sparsely populated website. The “About Us” page reads:
Oceans Edge Inc. (OE) is an engineering company founded in 2006 by wireless experts to design, build, deploy, and integrate Wireless Cyber Solutions.Our team is composed of subject matter experts in the following areas:
- Wireless Cyber Security
- Mobile Application Development
- Wireless Communication Protocols
- Wireless Network Implementation
- Lawful Intercept Technology
With this expertise, we deliver engineering services and wireless technology solutions in critical mission areas for our government and commercial customers.
Remote mobile spying
The patent is for a “Mobile device monitoring and control system.” The applicants summarize the technology thusly:
Methods and apparatus, including computer program products, for surreptitiously installing, monitoring, and operating software on a remote computer controlled wireless communication device are described.
In other words, the technology works to snoop on mobile phones by secretly installing itself on phone hardware. The targeted phone is thus compromised in two ways: first, the attacker can spy on all the contents of the phone; and second, the attacker can operate the phone from afar. That’s to say, it doesn’t just let the attacker read your text messages. It also potentially lets him write them.
The summary goes on:
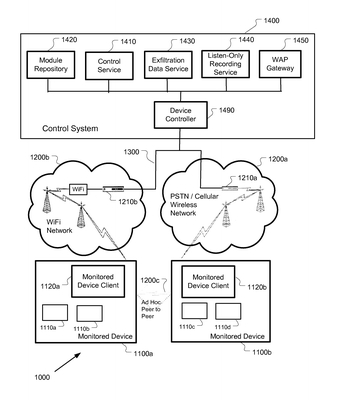
One aspect includes a control system for communicating programming instructions and exchanging data with the remote computer controlled wireless communication device. The control system is configured to provide at least one element selected from the group consisting of: a computer implemented device controller; a module repository in electronic communication with the device controller; a control service in electronic communication with the device controller; an exfiltration data service in electronic communication with the device controller configured to receive, store, and manage data obtained surreptitiously from the remote computer controlled wireless communication device; a listen-only recording service in electronic communication with the device controller; and a WAP gateway in electronic communication with the remote computer controlled wireless communication device.
The technology therefore also enables automated data storage of all of a phone’s activity in the attacker’s database. So if someone used this technology to spy on your phone, they would be able to use the Oceans’ Edge product to automatically store everything you do on it, to go back to later.
In case you aren’t sure who would want this kind of spook technology or why, Oceans’ Edge explains in the patent application:
A user’s employment of a mobile device, and the data stored within a mobile device, is often of interest to individuals and entities that desire to monitor and/or record the activities of a user or a mobile device. Some examples of such individuals and entities include law enforcement, corporate compliance officers, and security-related organizations. As more and more users use wireless and mobile devices, the need to monitor the usage of these devices grows as well. Monitoring a mobile device includes the collection of performance metrics, recording of keystrokes, data, files, and communications (e.g. voice, SMS (Short Message Service), network), collectively called herein “monitoring results“, in which the mobile device participates.
Mobile device monitoring can be performed using “over the air” (OTA) at the service provider, either stand-alone or by using a software agent in conjunction with network hardware such a telephone switch. Alternatively, mobile devices can be monitored by using a stand-alone agent on the device that communicates with external servers and applications. In some cases, mobile device monitoring can be performed with the full knowledge and cooperation of one of a plurality of mobile device users, the mobile device owner, and the wireless service provider. In other cases, the mobile device user or service provider may not be aware of the monitoring. In these cases, a monitoring application or software agent that monitors a mobile device can be manually installed on a mobile device to collect information about the operation of the mobile device and make said information available for later use. In some cases, this information is stored on the mobile device until it is manually accessed and retrieved. In other cases, the monitoring application delivers the information to a server or network device. In these cases, the installation, information collection, and retrieval of collected information are not performed covertly (i.e. without the knowledge of the party or parties with respect to whom the monitoring, data collection, or control, or any combination thereof, is desired, such as, but not limited to, the device user, the device owner, or the service provider). The use of “signing certificates” to authenticate software prior to installation can make covert installation of monitoring applications problematic. When software is not signed by a trusted authority, the software may not be installed, or the device user may be prompted for permission to install the software. In either case, the monitoring application is not installed covertly as required. Additionally, inspection of the mobile device can detect such a monitoring application and the monitoring application may be disabled by the device user. Alternatively, OTA message traffic may be captured using network hardware such as the telephone switch provided by a service provider. This requires explicit cooperation by the service provider, and provides covert monitoring that is limited to message information passed over the air. As a result, service provider-based monitoring schemes require expensive monitoring equipment, cooperation from the service provider, and are limited as to the types of information they can monitor.
Additional challenges are present when the monitoring results are transmitted from a mobile device. First, many mobile devices are not configured to transmit and receive large amounts of information. In some instances, this is because the mobile device user has not subscribed to an appropriate data service from an information provider. In other instances, the mobile device has limited capabilities.
Second, transmitting information often provides indications of mobile device activity (e.g. in the form of activity lights, battery usage, performance degradation).
Third, transmitting information wirelessly requires operation in areas of intermittent signal, with automated restart and retransmission of monitoring results if and when a signal becomes available.
Fourth, many mobile devices are “pay as you go” or have detailed billing enabled at the service provider. The transmission of monitoring results can quickly use all the credit available on a pre-paid wireless plan, or result in detailed service records describing the transmission on a wireless customer’s billing statement.
Lastly, stored monitoring results can take up significant storage on a mobile device and the stored materials and the use of this storage can be observed by the device user.
From the foregoing, it will be appreciated that effective covert monitoring of a mobile device requires the combination of several technologies and techniques that hide, disguise, or otherwise mask at least one aspect of the monitoring processes: the covert identification of the mobile devices to be monitored, the covert installation and control of the monitoring applications, and the covert exfiltration of collected monitoring results. As used herein, “covert exfiltration” refers to a process of moving collected monitoring results from a mobile device while it is under the control of another without their knowledge or awareness. Thus covert exfiltration processes can be those using stealth, surprise, covert, or clandestine means to relay monitoring data. “Collected monitoring results” as used herein includes any or all materials returned from a monitored mobile device to other devices, using either mobile or fixed points-of-presence. Examples of collected monitoring results include one or more of the following: command results, call information and call details, including captured voice, images, message traffic (e.g. text messaging, SMS, email), and related items such as files, documents and materials stored on the monitored mobile device. These materials may include pictures, video clips, PIM information (e.g. calendar, task list, address and telephone book), other application information such as browsing history, and device status information (e.g. device presence, cell towers/wireless transmitters/points-of-presence used, SIM data, device settings, location, profiles, and other device information). Additionally, the capability to covertly utilize a mobile device as a covertly managed camera or microphone provides other unique challenges.
Thus covert monitoring of a mobile device’s operation poses the significant technical challenges of hiding or masking the installation and operation of the monitoring application, its command and control sessions, hiding the collected monitoring results until they are exfiltrated, surreptitiously transmitting the results, and managing the billing for the related wireless services. The exemplary illustrative technology herein addresses these and other important needs.
Since we don’t know which agencies are using this technology or how, it’s hard to say to what extent this kind of secret monitoring is taking place in the US. We have some evidence suggesting that the FBI and DEA are using this tool (thanks, Chris Soghoian, for the tip). If those agencies really are using this technology, they should get warrants before they compromise anyone’s phone.
Is the government getting warrants to use this tool? We don’t know.
Oceans’ Edge Inc., like many purveyors of surveillance products, claims that its technology is only deployed for “lawful interception,” but it makes no claims about what that actually means. There’s no mention of judicial oversight, warrants, or any kind of due process. As I’ve written elsewhere on this blog, given the state of the law concerning surveillance in the digital age, we shouldn’t let our guard down simply because a company claims its surveillance tools are used lawfully. That’s because we do not know how these tools are being deployed, and yet we know that the state of surveillance law in the US at present grants the government wide latitude to infringe on our privacy in ways that are often improper or even unconstitutional.
In most cases (with a few notable exceptions), lawmakers haven’t worked to address this issue.
As we can see, surveillance technologies are developing rapidly. It’s past time for our laws to catch up.