Jan 26, 2012 | Black Technology, Video
I ran into a cool demonstration of non-contact heating. Huettinger, a German manufacturer of induction heating generators showed this ice cube running red-hot....
Jan 26, 2012 | Black Technology, Video
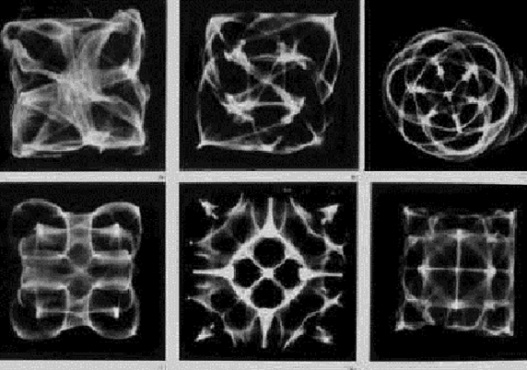
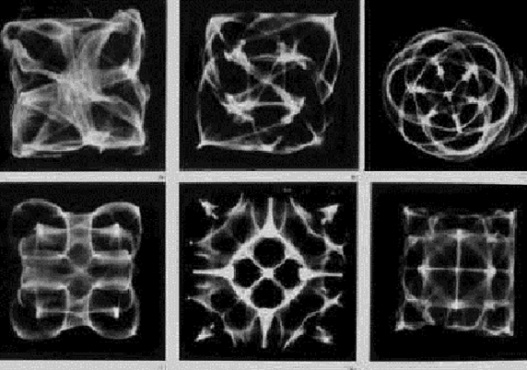
A sandy mixture will form various shapes and patterns naturally through the vibration of sound & frequency. Finally SOUND can be...

Jan 26, 2012 | Anonymous
Hello This Is Anonymous… This Message Is For You North Atlantic Treaty Organization… In Recent News On Your Report… Information and National Security” from General Rapporteur Lord Jopling of the UK discusses the potential good of social...

Jan 26, 2012 | Black Technology
Phones from Google, left, and Apple have “kill switches” built into them that allow the companies to remotely delete software. STORY HIGHLIGHTS Apple, Google and Microsoft all have kill switches built into their phone software Google has used the...

Jan 26, 2012 | Black Technology
From mysterious robotic space planes to giant spy satellites the size of school buses, space is teeming with secret American hardware meant to gaze down on insurgents, terrorists and, well, everybody on the third rock from the sun. For mere proles like you and me, it...
Jan 26, 2012 | Anonymous
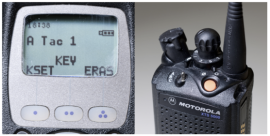
Visual Cryptography is a special encryption technique to hide information in images in such a way that it can be decrypted by the human vision if the correct key image is used. The technique was proposed by Naor and Shamir in 1994. Visual Cryptography uses two...

Jan 26, 2012 | Anonymous
Date: Wed, 9 Nov 2011 10:16:11 +0100 From: Eugen Leitl <eugen[at]leitl.org> To: cypherpunks[at]al-qaeda.net Subject: Re: [p2p-hackers] Verifying Claims of Full-Disk Encryption in Hard Drive Firmware —– Forwarded message from Tom Ritter...

Jan 26, 2012 | Government Agenda
CAMP WILLIAMS — Thursday’s groundbreaking for a $1.5 billion National Security Agency data center is being billed as important in the short term for construction jobs and important in the long term for Utah’s reputation as a technology center. “This...
Jan 26, 2012 | Globalist Corporations
Facebook really changed things up last week. Oh sure, it’s as disrespectful of my privacy as ever, but now it’s enlisted the entire web to help. So I’m done with anything that requires a Facebook login. Facebook made some big changes in terms of how...
Jan 26, 2012 | Anonymous, Black Technology
Donate $25 for two DVDs of the Cryptome collection of files from June 1996 to the present 16 April 2011. A sends: Roger Dingledine writes that the US Navy uses Tor for open source spying: http://idtrail.org/files/Dingledine%20-%20Tor.pdf 28 March 2011. Add comments...
Jan 26, 2012 | Anonymous, Black Technology
Where governments get their toolsRandom Document Documents obtained by The Wall Street Journal open a rare window into a new global market for the off-the-shelf surveillance technology that has arisen in the decade since the terrorist attacks of Sept. 11, 2001. The...

Jan 26, 2012 | Black Technology, WAR: By Design
When the pilotless, wing-shaped warplane lifted off a runway at California’s Edwards Air Force Base for the first time on the morning of April 27, it was like the resurrection of the dead. The Boeing Phantom Ray — one of the most advanced drones ever built — came...
Jan 26, 2012 | Black Technology
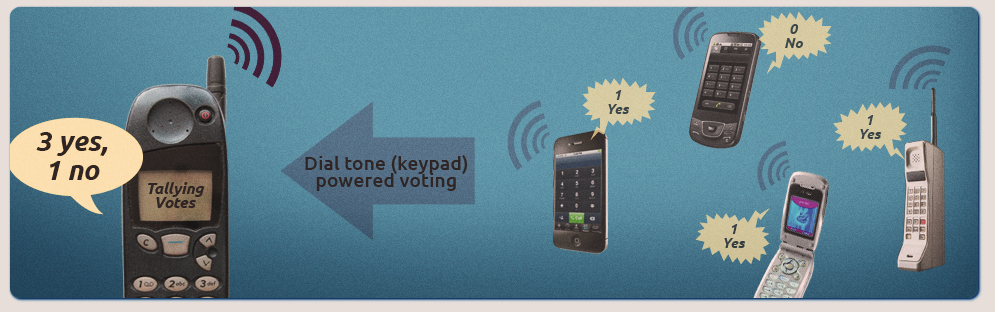
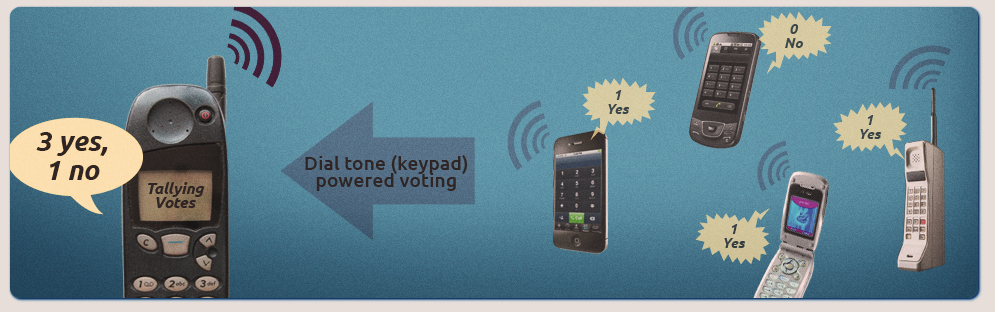
A phone-powered, distributed voice and voting system for the #Occupy Movement call 917-719-2006 The People’s Mic works well for small General Assemblies, but in larger GAs, multiple echoes of the speaker’s words is hard to follow. The People’s Skype...

Jan 26, 2012 | Black Technology
Australia’s Largest ISPs Agreed to Voluntary Web Censorship In 2011, Australia moved closer to becoming one of the few Western democracies with active internet content filtering when its two largest internet service providers — Telstra and Optus — confirmed they...
Jan 26, 2012 | Black Technology
Expensive high-tech digital radios used by the FBI, Secret Service, and Homeland Security are designed so poorly that they can be jammed by a $30 children’s toy, CNET has learned. A GirlTech IMME, Mattel’s pink instant-messaging device with a miniature...
Jan 26, 2012 | Black Technology, Video
Scientists demonstrate the ability to use an MRI machine to read brainwaves and brain activity and recreate movies watched by test subjects. I previously reported on scientists demonstrating the ability to upload, download and transfer memories and learned behavior...
Jan 26, 2012 | Black Technology
By Grazyna Fosar and Franz Bludorf www.ryze.com/view.php?who=vitaeb THE HUMAN DNA IS A BIOLOGICAL INTERNET and superior in many aspects to the artificial one. Russian scientific research directly or indirectly explains phenomena such as clairvoyance, intuition,...
Jan 26, 2012 | Black Technology, Video
Jan 26, 2012 | Anonymous, Black Technology, Video
The Android developer who raised the ire of a mobile-phone monitoring company last week is on the attack again, producing a video of how the Carrier IQ software secretly installed on millions of mobile phones reports most everything a user does on a phone. Though the...

Jan 26, 2012 | Black Technology
When will humanity reach Singularity, that now-famous point in time when artificial intelligence becomes greater than human intelligence? It is aptly called the Singularity proponents like Ray Kurzweil: like the singularity at the center of a black hole, we have no...
Jan 26, 2012 | Black Technology
A graduate level course Richard Fitzpatrick Associate Professor of Physics The University of Texas at Austin Introduction Major sources Fundamental concepts The breakdown of classical physics The polarization of photons The fundamental principles of...
Jan 26, 2012 | Black Technology
This is the web portal to receive news and information about Andrew D. Basiago’s quest to lobby the US government to disclose its teleportation secret so that teleportation can be adopted on a global basis to help humanity achieve planetary sustainability in the 21st...
Jan 26, 2012 | Anonymous
The Phantom protocol is a system for decentralized anonymization of generic network traffic. It has been designed with the following main goals in mind: 1. Completely decentralized. – No critical or weak points to attack or put (il)legal pressure on. 2. Maximum...
Jan 26, 2012 | Government Agenda
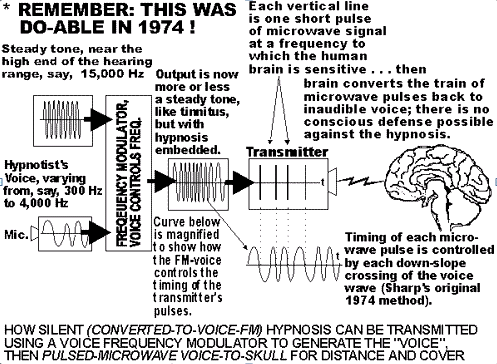
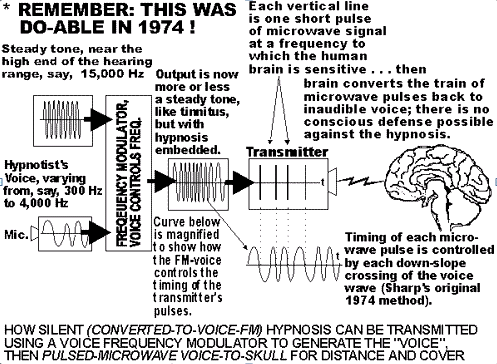
A lawsuit filed against the U.S. National Security Agency reveals a frightening array of technologies and programs designed to keep tabs on individuals. . John St Clair Akwei vs National Security Agency Ft George G. Meade, MD, USA (Civil Action 92-0449) . The...
Jan 26, 2012 | Black Technology
On April 22, 1993, both BBC1 and BBC2 showed on their main evening news bulletins a rather lengthy piece concerning America’s latest development in weaponry – the non-lethal weapons concept. David Shukman, BBC Defense Correspondent interviewed (Retired) U.S....