Jan 26, 2012 | Black Technology
Details of an emerging data-mining and intelligence-analysis program reminiscent of the Pentagon’s controversial Total Information Awareness (TIA) project emerged yesterday, U.S. Trade & Aid Monitor has discovered. Similar to TIA, which Congress in 2003 de-funded...
Jan 26, 2012 | Black Technology, Video
Dec. 19 – Software developed for closed-circuit television systems can identify individuals and track them across entire networks of cameras. Joel Flynn reports. http://www.youtube.com/watch?v=zsf1VhZ9L7c
Jan 26, 2012 | Black Technology
Large-scale AFIS and multi-biometric identification MegaMatcher technology is intended for large-scale AFIS and multi-biometric systems developers. The technology ensures high reliability and speed of biometric identification even when using large databases....
Jan 26, 2012 | Anonymous
Namecoin is a domain name system based on Bitcoin. It extends Bitcoin to add transactions for registering, updating and transferring names. The idea behind this is to provide an alternative to the existing DNS system where names can be taken from their owners by...

Jan 26, 2012 | Black Technology
“Josie and the Pussycats” is a “girl band movie” aimed at children and young adolescents, especially young girls. At first glance, the flick seems to be one of those generic, God-awful teen movies. However, a closer look reveals how its overall tone and message are in...
Jan 26, 2012 | Black Technology, Video
Amazing CGI visualization of molecular biology’s central dogma. It shows animations of DNA coiling, replication, transcription and translation. It was created by Drew Berry of the Walter and Eliza Hall Institute of Medical Research...

Jan 26, 2012 | Nature Body Mind, Video
Spontaneous Evolution Has Arrived! by Gregg Prescott, M.S. . www.in5d.com www.maya12-21-2012.com www.HolisticCancerResearch.com Spontaneous evolution has occurred in history at specific increments in time. What causes these changes? How do these changes affect...
Jan 26, 2012 | Black Technology, Video
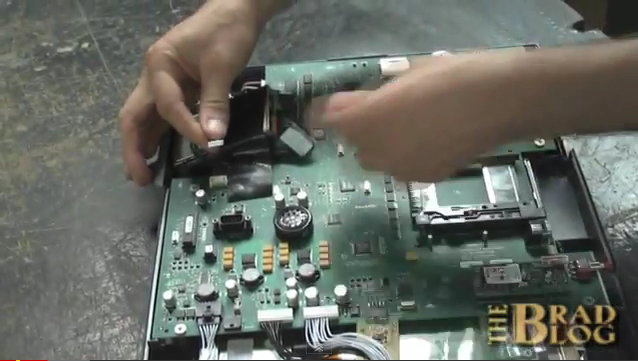
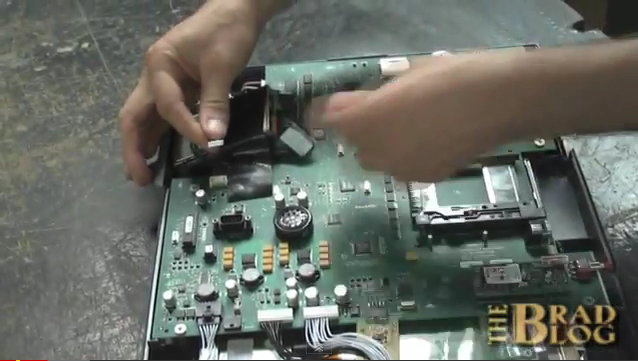
Man-in-the-Middle Remote Attack on Diebold Touch-screen Voting Machine The Vulnerability Assessment Team (VAT) at the U.S. Dept. of Energy’s Argonne National Laboratory in Illinois has managed to hack a Diebold Accuvote touch-screen voting machine. Voting...

Jan 26, 2012 | Black Technology
Physicists Proposed That the Future Could Be Preventing Higgs Boson Discovery In 2009, two respected physicists put forward one of the most unusual hypotheses in modern particle physics. Danish physicist Holger Bech Nielsen and Japanese physicist Masao Ninomiya...
Jan 26, 2012 | Central Banking Elite
The cowardly Japanese Prime Minister Naoto Kan handed 60 trillion yen (about 700 Billion US$) over to the Federal Reserve Board crime syndicate immediately after his country was attacked with HAARP and nuclear terror, according to Japanese security police sources. The...
Jan 26, 2012 | Activism, Black Technology
On return to Europe from the 2008 NEXUS Conference in Australia, flying out of Sydney, we stopped off in Thailand to visit a close friend who lives on the island of Koh Samui. Samui is well known as a travelers’ international crossroads, and is also a place...

Jan 26, 2012 | Anonymous
The Hacker Known as Kayla and the HBGary Federal Breach In early 2011, a hacker operating under the alias “Kayla” claimed to be a 16-year-old girl who split her time between ordinary teenage life and participating in operations with Anonymous, the...

Jan 26, 2012 | Anonymous
Dissident members of the internet hacktivist group Anonymous, tired of what they call the mob’s “unpatriotic” ways, have provided law enforcement with chat logs of the group’s leadership planning crimes, as well as what they say are key...

Jan 26, 2012 | Black Technology
The world is changing fast–maybe faster than we ever thought. And within five years, science fiction is going to turn into non-fiction. We’ll be able to read each other’s minds, forget all our passwords, and create all our own homes’ energy....
Jan 26, 2012 | Black Technology, Video
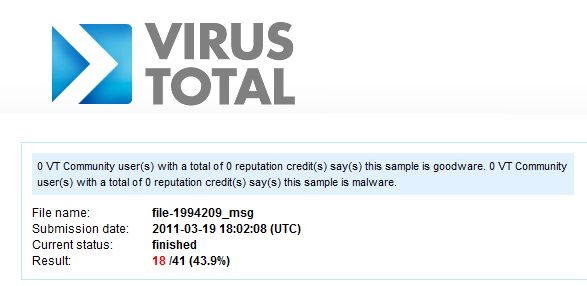
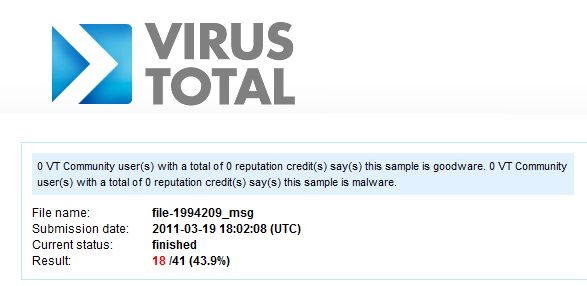
RSA was hacked in March. This was one of the biggest hacks in history. The current theory is that a nation-state wanted to break into Lockheed-Martin and Northrop-Grumman to steal military secrets. They couldn’t do it, since these companies were using RSA...

Jan 26, 2012 | Anonymous
A Hacking Group That Embarrassed the Security Industry In the summer of 2011, a hacktivist collective calling itself LulzSec — short for “Lulz Security,” with “lulz” referring to amusement derived from disrupting others — conducted a rapid-fire...

Jan 26, 2012 | Black Technology
Speaking at the Chaos Computer Club (CCC) Congress in Berlin on Tuesday, a pair of researchers demonstrated a start-to-finish means of eavesdropping on encrypted GSM cellphone calls and text messages, using only four sub-$15 telephones as network “sniffers,” a laptop...
Jan 26, 2012 | Globalist Corporations
Google continued to demonstrate its commitment to transparency on Monday by releasing fresh statistics on the number of times it has disclosed private user data to a government, or removed content at government request. The country-by-country report covers the second...
Jan 26, 2012 | Black Technology
GE Developed a Faster Holographic Disc Format In 2011, General Electric announced a significant breakthrough in holographic data storage technology. At an IEEE symposium in Hawaii, the company revealed a new micro-holographic material that was 100 times more sensitive...
Jan 26, 2012 | Black Technology
In June 2011, a virulent strain of E. coli swept across Europe, killing 22 people and sickening over 2,153 others with severe symptoms including bloody diarrhea and hemolytic uremic syndrome, a condition that causes kidney failure. The outbreak was eventually traced...

Jan 26, 2012 | Black Technology, Government Agenda
The FBI CIPAV: A Digital Surveillance Tool The FBI developed a computer surveillance program known as the Computer and Internet Protocol Address Verifier, or CIPAV, designed to covertly monitor suspects through their own machines. Court documents from the Josh...
Jan 26, 2012 | Black Technology
Nuclear Engineer, Mehran Tavakoli Keshe, has came forward as being the developer of the technology being used in Iran’s new “flying saucer.” His technology is claimed to harness magnetism and gravity to allow travel throughout the solar system and beyond. On March...
Jan 26, 2012 | Black Technology, Government Agenda
Encryption, Warrants And The FBI Last Thursday, the House Judiciary Committee held a hearing focused on law enforcement surveillance of modern Internet services. Although both the New York Times and CNET have stories on the hearing, I don’t think either...
Jan 26, 2012 | Black Technology
One of the demands of the Egyptian revolution was to demolish one of the well-known security services for torture, grave human rights violations and spying on activists which is the State Security Investigations (SSI) and to have its officers set onto trials. Few...

Jan 26, 2012 | Black Technology
by Grazyna Fosar and Franz Bludorf Russian DNA Discoveries: Original version THE HUMAN DNA IS A BIOLOGICAL INTERNET and superior in many aspects to the artificial one. The latest Russian scientific research directly or indirectly explains phenomena such as...