Aug 15, 2015 | Enlightened Influences, Hollywood Programming
John Oliver is an English comedian who first attracted US attention through his work on The Daily Show with Jon Stewart. In April 2014, he began taping episodes of Last Week Tonight with John Oliver, a weekly half-hour program that satirizes news and current events....

Jul 15, 2015 | Black Technology, Leaks
Major Security Flaw Discovered in School Monitoring Software Used by Thousands of Students Impero Education Pro, one of the most widely deployed student monitoring and internet restriction tools in the United Kingdom, was found to contain a critical security...

Mar 19, 2015 | Anonymous, Whistleblowers & Dissidents
Anonymous radio host know as Lorax aka Adam Bennett Anon was arrested (full article). Everybody who has known Adam ‘Lorax’ Bennett aka Adam Bennett Anon knows he’s an awesome anon. Furthermore, the article now let us know he was also involved in his local...
Mar 13, 2015 | Events & Assassinations, Whistleblowers & Dissidents
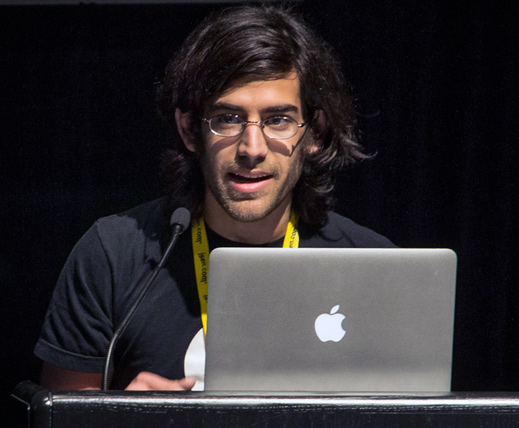
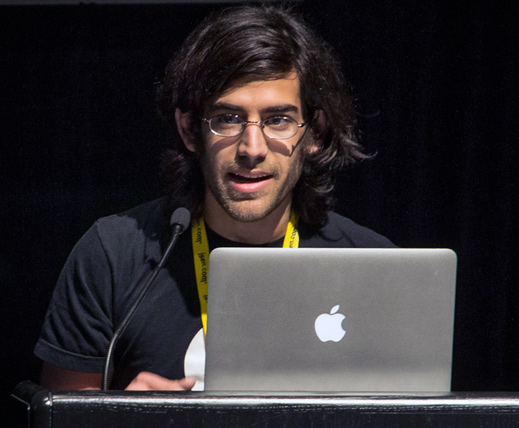
Aaron Swartz was a computer programmer and Internet activist who is often referred to as the third founder of Reddit. “”I don’t think I have any particular technical skills. I just got a really large head start.”” -Aaron Swartz Early Years Aaron...

Feb 25, 2015 | Leaks, News
AMERICAN AND BRITISH Leaked: NSA Spies hacked into the internal computer network of the largest manufacturer of SIM cards in the world, stealing encryption keys used to protect the privacy of cellphone communications across the globe, according to top-secret documents...
Feb 16, 2015 | Black Technology, News
There is often times a trade-off between security and convenience. With Home Hacks the more easily you can access your personal data, the easier someone else can too, making anything that you put online a potential target for hackers. A growing source of concern for...

Feb 13, 2015 | 2020 Relevant, Government Agenda, News
Federal Judge Dismissed Challenge to NSA Surveillance on Secrecy Grounds In February 2015, U.S. District Judge Jeffrey White ruled in favor of the National Security Agency in the landmark case Jewel v. NSA, dismissing a challenge to the government’s mass...
Jan 31, 2015 | Government Agenda, News
Understanding the Limited Hangout: A Framework for Intelligence Analysis In the vocabulary of intelligence tradecraft, few concepts are as important — or as poorly understood by the general public — as the limited hangout. The term describes an operation in which an...

Dec 11, 2014 | 2020 Relevant, Leaks, Whistleblowers & Dissidents
Barrett Brown is an American journalist, essayist and satirist. He is often referred to as an unofficial spokesperson for the hacktivist collective Anonymous, a label he disputes. He is credited with the creation of Project PM, a research outfit and information...
Dec 10, 2014 | Whistleblowers & Dissidents
Edward Joseph “Ed” Snowden is an American computer professional who leaked classified information from the National Security Agency, starting in June 2013.Edward Joseph “Ed” Snowden is an American computer professional who leaked classified...
Dec 9, 2014 | Leaks, Whistleblowers & Dissidents
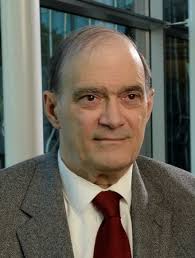
William Binney William Edward Binney is a former highly placed intelligence official with the United States National Security Agency turned whistleblower who resigned on October 31, 2001, after more than 30 years with the agency. We need more truthers like this guy....

Dec 9, 2014 | Leaks, Whistleblowers & Dissidents
Thomas Drake is a former senior executive of the U.S. National Security Agency, a decorated United States Air Force and United States Navy veteran, and a whistleblower.is a former senior executive of the U.S. National Security Agency, a decorated United States Air...

Dec 9, 2014 | 2020 Relevant, Taboo Terminology
The FBI began COINTELPRO—short for Counterintelligence Program—in 1956 to disrupt the activities of the Communist Party of the United States. In the 1960s, it was expanded to include a number of other domestic groups, such as the Ku Klux Klan, the Socialist Workers...
Nov 13, 2014 | 2020 Relevant, Anonymous, News
Statement of Purpose I have been observing the hacker and hacktivist communities, at times very closely, for many years. The exact definition of “hacker” and “hacktivist” varies from author to author, so I shall make my interpretation of these words very clear. Let us...

Nov 3, 2014 | Government Agenda, News
The Encryption Debate: FBI Claims vs. Whistleblower Promises In October 2014, FBI Director James Comey delivered a carefully crafted address at the Brookings Institution, warning that robust encryption technologies were causing American intelligence agencies to...

Sep 21, 2014 | Abuses of Power, Black Technology, Leaks
Government Threatened Yahoo With Daily Fines Over PRISM Compliance In September 2014, approximately 1,500 pages of previously classified court documents revealed how the United States government coerced Yahoo into participating in the NSA’s PRISM surveillance...

Jul 23, 2014 | Activism, DCMX Radio, Video
Max Maverick breaks down everything we know, don’t know, and should be asking about this mainstream media ‘circus’ that has become of the Snowden NSA Leak Disclosure. Major Players – Hidden Hands Past NSA Leaks & Leakers Advanced...

Jul 12, 2014 | 2020 Relevant, News
Since the September 11, 2001 attacks, an estimated 5,000 American civilians have been killed by police officers — a figure roughly equivalent to the number of U.S. soldiers killed in the Iraq war during the same period. The statistics have prompted difficult...

Jul 12, 2014 | Abuses of Power, News
Shortly after the Snowden leaks began exposing the NSA’s massive collection efforts, the New York Times uncovered the DEA’s direct access to AT&T telecom switches (via non-government employee “analysts” working for AT&T), from which it...

Jul 2, 2014 | Abuses of Power, News
The bulk phone records program under the Patriot Act drew intense public backlash against the National Security Agency for years. But a far more expansive and arguably more invasive surveillance apparatus deserved equal scrutiny: the warrantless search capabilities...
May 19, 2014 | Abuses of Power, Black Technology, Leaks
Understanding NSA Naming Conventions The National Security Agency and related U.S. intelligence organizations use a structured system of nicknames and codewords to identify their surveillance programs, tools, databases, operations, and targets. These designations...

May 14, 2014 | Globalist Corporations, Video, WAR: By Design
War For those who are completely new to the Palantir Platform or could simply use a refresher, this talk will start from scratch and provide a broad overview of Palantir’s origins and mission. A live demonstration of the product will help to familiarize...

Dec 9, 2013 | Government Agenda, Leaks, News
How Intelligence Agencies Infiltrated Virtual Worlds A joint investigation by The New York Times, The Guardian, and ProPublica — drawing on classified documents provided by former NSA contractor Edward Snowden — revealed that American and British intelligence services...

Dec 7, 2013 | Central Banking Elite, News
When Bitcoin first emerged, it was widely characterized as a threat to the established financial order. Governments, banks, and mainstream media initially treated cryptocurrency with suspicion and hostility. Yet within a few years, that posture shifted dramatically....
Sep 19, 2013 | DCMX Radio
Show Recap On the September 19, 2013 edition of Decrypted Matrix Radio, Max delivered an urgent broadcast in the aftermath of the Washington Navy Yard shooting, examining the false flag indicators, the shooter’s psychiatric medication history, and the latest NSA...