Apr 9, 2013 | Abuses of Power, News
The United States government routinely classifies documents to protect genuine national security interests. However, the classification system also provides a convenient mechanism for officials to bury materials that would expose embarrassing, unethical, or outright...

Mar 20, 2013 | Abuses of Power, Survivalism
Over the past several decades, a wave of controversial legislation has systematically weakened constitutional protections for ordinary Americans. Laws like the Military Commissions Act, the Patriot Act (both iterations), the John Warner Defense Authorization Act, and...

Mar 20, 2013 | Abuses of Power, Survivalism
A common Rule of Thumb….when ever a bureaucrat asks you a question, a safe “answer” is to ask them a question in return. Be polite, but be firm. They often want to extract information out of you without you being the wiser. There is no transparency...
Jan 16, 2013 | Abuses of Power, News
Executive Actions on Gun Safety Following Mass Shootings In January 2013, President Barack Obama signed a series of executive actions aimed at reducing gun violence in the United States. The measures came in the wake of the Sandy Hook Elementary School shooting in...

Dec 28, 2012 | Abuses of Power, Globalist Corporations, News
Facebook Purged Pro-Second Amendment and Alternative Media Accounts In late December 2012, Facebook conducted what appeared to be a coordinated removal of accounts and pages associated with pro-second amendment advocacy and alternative media commentary. The purge...

Dec 19, 2012 | Abuses of Power, Events & Assassinations, News
The Documented Link Between Disarmament and State Violence Throughout the twentieth century, a disturbing pattern emerged across multiple continents: governments that stripped their populations of firearms often followed with campaigns of mass persecution. The...

Dec 19, 2012 | Abuses of Power, News, Video
http://youtu.be/N4CT4boLPrU Maybe they should prosecute the MSM. Posting Truth,Info,Questions or not believing official story Related to Mass Shooting In Newtown Connecticut at Sandy Hook Elementary School will result in arrests and prosecutions of perpetrators of...

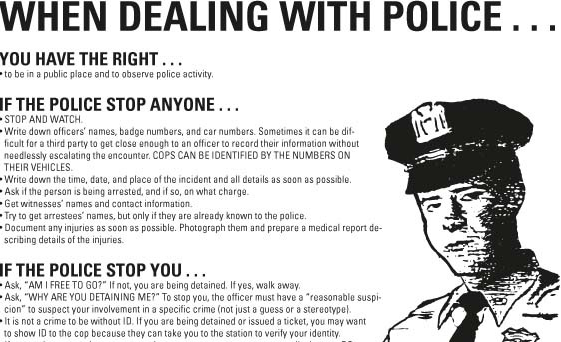
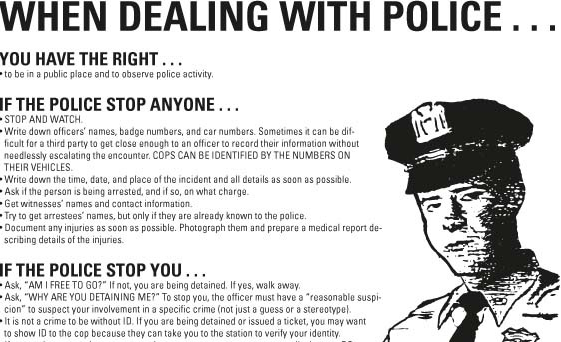
Dec 6, 2012 | Abuses of Power
Conversations about police misconduct often hit the same wall: disbelief. People who have never had a negative encounter with law enforcement struggle to accept that officers can operate with so few constraints. For anyone working in criminal defense, though, that...
Nov 28, 2012 | Abuses of Power

Nov 8, 2012 | Abuses of Power
Army Prosecutors Unveil Case Against One-Star General In November 2012, Army prosecutors at Fort Bragg, North Carolina opened an Article 32 hearing against Brigadier General Jeffrey A. Sinclair, a 27-year veteran of the United States military. The 50-year-old officer...
Nov 4, 2012 | Abuses of Power

Nov 1, 2012 | Abuses of Power
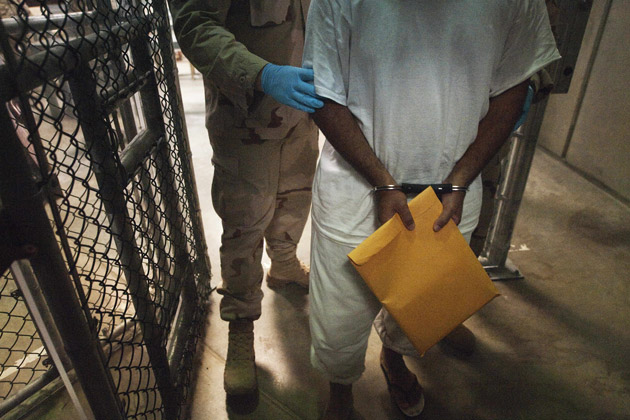
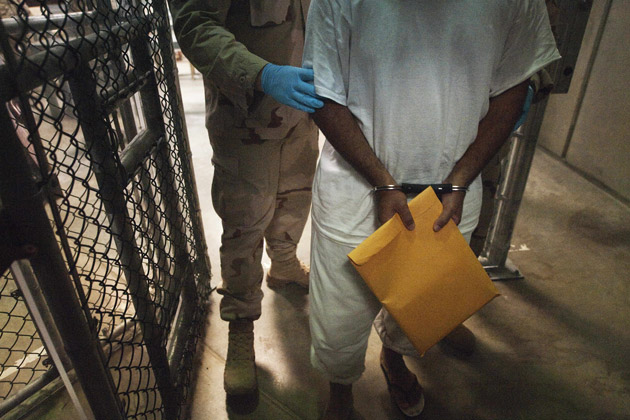
Pre-Trial Hearings Expose Government Secrecy Over Torture In late October 2012, Khalid Sheikh Mohammed and his co-defendants in the 9/11 terror case appeared for a pre-trial hearing at Guantanamo Bay. Army Colonel James L. Pohl presided over the military commission...

Oct 31, 2012 | Abuses of Power, Activism
Whether you view Barrett Brown as a folk hero or a reckless provocateur, most observers agreed on one thing in late 2012: the statements that led to his arrest and federal indictment were profoundly unwise. His detractors felt vindication, while his supporters rallied...

Oct 29, 2012 | Abuses of Power, Activism
Khan Removed From Flight and Questioned About Drone Strike Stance Imran Khan, the former Pakistan cricket captain and leader of the Pakistan Movement for Justice party (PTI), was removed from an international flight traveling from Canada to New York in October 2012....

Oct 28, 2012 | Abuses of Power
A British Iraq war veteran was made redundant just 72 hours before he would have qualified for a full Army pension, exposing what critics described as a pattern of cost-cutting at the expense of long-serving military personnel. Three Days Short After Nearly 18 Years...

Oct 24, 2012 | Abuses of Power
About 300 people have been wrongfully convicted and exonerated in the U.S. thanks to DNA evidence. But overlooked in those stories are the accounts of jurors who unwittingly played a role in the injustice. One of those stories is playing out in Washington, D.C., where...

Oct 24, 2012 | Abuses of Power, WAR: By Design
Romney Endorsed Obama’s Drone Strategy During the 2012 Foreign Policy Debate During the October 2012 foreign policy debate, Mitt Romney essentially gave his stamp of approval to President Obama’s use of unmanned aerial strikes. Regardless of which...

Oct 24, 2012 | Abuses of Power, Events & Assassinations
What Is the Disposition Matrix? In October 2012, reporting revealed that the Obama administration had spent two years secretly building what officials called the “disposition matrix” — a next-generation database designed to institutionalize and expand the...
Oct 24, 2012 | Abuses of Power, Activism, News
In a case that drew national attention to the tension between government secrecy and accountability, former CIA officer John Kiriakou accepted a plea deal and received a 30-month prison sentence for disclosing classified information related to the agency’s...
Oct 13, 2012 | Abuses of Power, News
The Freedom of Information Act (FOIA) stands as one of the most important transparency mechanisms in American democracy, granting citizens the ability to request and obtain records about government operations. While the law includes limited exemptions allowing...

Oct 10, 2012 | Abuses of Power, News
A school district in Texas came under fire earlier this year when it announced that it would require students to wear microchip-embedded ID cards at all times. Now students who refuse to be monitored say they are feeling the repercussions. Since October 1, students at...
Oct 10, 2012 | Abuses of Power, WAR: By Design
The Government’s Bid to Classify Detainees’ Own Experiences In 2012, the U.S. government sought to prevent the defendants in the 9/11 military commission trial from publicly describing their own experiences in CIA custody. A newly unsealed motion proposed...

Oct 4, 2012 | Abuses of Power, Government Agenda
Senate Investigation Exposes Massive Waste at DHS Fusion Centers A damning 107-page report released by the Senate Permanent Subcommittee on Investigations revealed that the Department of Homeland Security spent an estimated $289 million to $1.4 billion on regional...
Oct 3, 2012 | Abuses of Power, News
In October 2012, a federal appeals court extended a temporary stay against a district court ruling that had blocked the government from enforcing a controversial indefinite detention provision contained in the National Defense Authorization Act (NDAA) of 2011. Appeals...
Sep 27, 2012 | Abuses of Power, Activism, News
In September 2012, the Obama administration launched an aggressive legal counterattack against a federal court ruling that struck down one of the most controversial provisions in recent American legislative history: the indefinite military detention clause of the 2011...