Apr 28, 2012 | Abuses of Power
The FBI’s ambitions to monitor social media in real time raise fundamental questions about the balance between national security and individual privacy. In early 2012, the bureau began soliciting the technology industry for help building an open-source...

Apr 27, 2012 | WAR: By Design
Two independent investigations published in early 2012 presented substantial new evidence that CIA drone strikes in Pakistan’s tribal areas were killing civilians at higher rates than official accounts acknowledged. Associated Press Field Investigation The...
Apr 27, 2012 | WAR: By Design
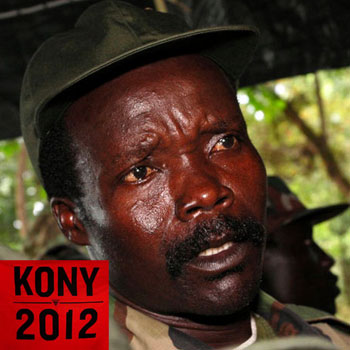
In early 2012, the Kony 2012 viral campaign generated unprecedented public attention toward Joseph Kony, leader of the Lord’s Resistance Army in Uganda. While the campaign presented itself as a humanitarian effort to bring a war criminal to justice, a number of...

Apr 27, 2012 | Abuses of Power, News
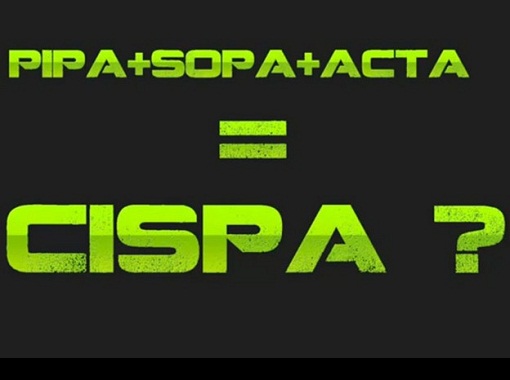
What Was CISPA and Why Did It Matter? The Cyber Intelligence Sharing and Protection Act (H.R. 3523) emerged in late 2011 as a proposed amendment to the National Security Act of 1947. Introduced by Representatives Mike Rogers (D-MI) and C.A. “Dutch”...

Apr 26, 2012 | Abuses of Power, News
Journalists Targeted After Investigating Pentagon Contractors In 2012, two USA Today employees became the targets of a coordinated online disinformation and harassment campaign shortly after making inquiries to intelligence contractors with ties to the U.S. military....

Apr 26, 2012 | Abuses of Power
Obama Administration Sought to Shield NSA Surveillance Law From Court Review In 2012, the Obama administration asked the Supreme Court to dismiss a legal challenge to one of the most expansive surveillance statutes in American history — the FISA Amendments Act of...
Apr 26, 2012 | Abuses of Power, News
CISPA: The Cyber Intelligence Sharing and Protection Act Explained In April 2012, the Cyber Intelligence Sharing and Protection Act (CISPA), formally designated H.R. 3523, advanced through the U.S. Congress amid fierce debate over digital privacy and national...

Apr 26, 2012 | WAR: By Design
Pentagon Pushes for Military Operatives Under Commercial Cover The Pentagon submitted a formal proposal to Congress seeking expanded legal authority that would allow U.S. military personnel to operate overseas under the guise of civilian business activities. The...
Apr 26, 2012 | Abuses of Power, News, Video
Senate Bill 1813 and Its Hidden Implications for Gun Owners In 2012, the U.S. Senate passed Bill 1813, officially titled the “Moving Ahead for Progress in the 21st Century Act.” While ostensibly a transportation bill, analysts who examined its 1,676 pages...

Apr 25, 2012 | Events & Assassinations
Throughout history, individuals who possessed critical firsthand knowledge of significant events have met untimely and suspicious ends. Whether they were eyewitnesses to assassinations, insiders within government intelligence programs, or journalists exposing...

Apr 25, 2012 | Abuses of Power, News
LOS ANGELES (CBS) — A bill authored by a Southland lawmaker that could potentially allow the federal government to prevent any Americans who owe back taxes from traveling outside the U.S. is one step closer to becoming law. Senate Bill 1813 was introduced back in...

Apr 25, 2012 | Government Agenda, Leaks
The FBI and Department of Justice produced a series of 25 flyers under the “Communities Against Terrorism” initiative, designed to be distributed to businesses across a wide range of industries. These documents instructed employees and business owners on...

Apr 24, 2012 | Abuses of Power
The Private Prison Industry in the United States The American prison system has long functioned as a profit-driven enterprise. Private corporations operate over 200 correctional facilities across the country, and many of these companies are publicly traded on the New...

Apr 24, 2012 | Events & Assassinations
Did individuals with advance knowledge of the September 11, 2001 attacks exploit financial markets for profit? An investigation into put option trading, surveillance software, and the paper trail that regulators chose not to follow. PROMIS Software: The Intelligence...

Apr 24, 2012 | Black Technology, Government Agenda
The NSA’s Massive Expansion After 9/11 In a period of extraordinary growth, the National Security Agency embarked on a construction spree that reshaped the American intelligence landscape. NSA Director General Keith Alexander traveled the country inaugurating...

Apr 24, 2012 | Events & Assassinations, News
The Kandahar Massacre: Official Narrative vs. Afghan Eyewitness Accounts The question is as old as American military controversies themselves: was a horrific act of violence the work of a single disturbed individual, or were there accomplices who have never been...

Apr 24, 2012 | Abuses of Power, Government Agenda
A Filmmaker Detained Dozens of Times at U.S. Borders Laura Poitras, an acclaimed documentary filmmaker whose work examined the consequences of the War on Terror, was subjected to systematic harassment by the Department of Homeland Security every time she returned to...

Apr 24, 2012 | Abuses of Power, News
In the spring of 2012, Michigan’s Department of Natural Resources (DNR) rolled out a sweeping Invasive Species Order (ISO) that effectively reclassified heritage-breed pigs — the same animals small family farms had raised for generations — as illegal...

Apr 24, 2012 | Abuses of Power, News
How Law Enforcement Bypassed iPhone Passcodes A four-digit iPhone passcode might deter a casual snoop, but in 2012, law enforcement agencies had access to commercial tools that could crack that security in remarkably little time. A Swedish firm called Micro...
Apr 24, 2012 | News, Video, WAR: By Design
http://www.youtube.com/watch?v=fuWItcSRrM8 “We want the Syrian Army to come into Homs.” “We want the Syrian Army posted on the roofs of the houses, with helicopters and tanks.” “Stop these snipers from killing us.” ~ The Residents...
Apr 16, 2012 | Abuses of Power, Globalist Corporations
H.R. 3523 – Letters of Support AT&T Boeing BSA Business Roundtable CSC COMPTEL CTIA – The Wireless Association Cyber, Space & Intelligence Association Edison Electric EMC Exelon Facebook The Financial Services Roundtable IBM Independent Telephone...

Apr 16, 2012 | Abuses of Power, News
Executive Order on National Defense Resources Preparedness: What It Actually Claims In March 2012, President Obama signed an Executive Order titled “National Defense Resources Preparedness” that significantly expanded the claimed scope of executive...
Apr 16, 2012 | Events & Assassinations
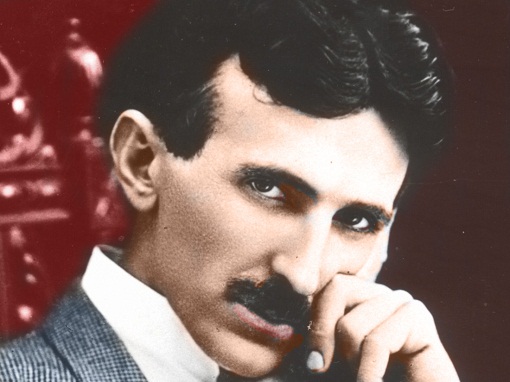
The Mysterious Death of a Visionary Inventor Nikola Tesla stands among the most extraordinary minds in human history. Widely regarded by modern scholars as “the father of physics,” “the man who invented the twentieth century,” and “the...

Apr 16, 2012 | WAR: By Design
The push for military confrontation with Iran has been a recurring theme in Western foreign policy for decades. Yet a closer examination of historical context, intelligence assessments, and geopolitical realities reveals a far more complex picture than the one...

Apr 16, 2012 | Abuses of Power
Arizona HB 2549: Criminalizing Online Speech In 2012, the Arizona legislature passed House Bill 2549, a measure that would have expanded the state’s existing telephone harassment statute to cover the internet and all electronic communications. The bill’s...