Jul 12, 2012 | Abuses of Power, News
UK Law Criminalizes Failure to Surrender Encryption Keys Under the Regulation of Investigatory Powers Act 2000, the United Kingdom made it a criminal offense to fail to produce encryption keys when demanded by authorities. The law, specifically Section 53 of the act,...

Jul 11, 2012 | Black Technology, News
In the near future, the U.S. Department of Homeland Security could gain the ability to learn virtually everything about your physical person — your clothing, your belongings, even your recent meals — using an advanced laser-based molecular scanner that operates from...

Jul 10, 2012 | Activism, Government Agenda
EFF Asks Court to Reject Stale State Secret Arguments So Case Can Proceed San Francisco – Three whistleblowers – all former employees of the National Security Agency (NSA) – have come forward to give evidence in the Electronic Frontier Foundation’s...

Jun 12, 2012 | News, WAR: By Design
The Intelligence Community’s Evolving Position on September 11 The events of September 11, 2001, continue to generate fierce debate more than a decade later. What has changed significantly over time is the stance of credible voices within the military and...
Jun 6, 2012 | Globalist Corporations, Government Agenda
Careless mistake reveals subversion of Windows by NSA? A CARELESS mistake by Microsoft programmers has revealed that special access codes prepared by the US National Security Agency have been secretly built into Windows. The NSA access system is built into every...
May 31, 2012 | Activism, News, Satire, Video
Juice Rap News: Episode XIII – A NEWS HOPE. It is a time of corporate war; deprived of a reliable media the people of Planet Earth are kept misinformed and in a state of perpetual conflict. Is an honest Fourth Estate the only Force than can restore peace and...

May 31, 2012 | Anonymous
>>> FBI BITCOIN REPORT – APRIL 2012 <<<< The FBI sees the anonymous Bitcoin payment network as an alarming haven for money laundering and other criminal activity — including as a tool for hackers to rip off fellow Bitcoin users. That’s...

May 24, 2012 | News
When the NYPD cleared the Zuccotti Park encampment in downtown Manhattan in November 2011, many observers declared the Occupy movement effectively finished. Mainstream media coverage dwindled, and commentators attributed the decline to what they characterized as a...

May 21, 2012 | Black Technology
Modern Surveillance Cameras Can Read Phone Screens From a Distance Surveillance camera technology has advanced to the point where operators can zoom in on individuals in a crowd and read the text displayed on their phone screens. This capability was demonstrated...

May 19, 2012 | Anonymous, Government Agenda
When the Occupy Wall Street encampment in Lower Manhattan was barely a month old, federal and local law enforcement agencies were already receiving inside intelligence about the movement’s plans. The source was not an undercover officer or a formal informant —...

May 10, 2012 | Abuses of Power, News
Michigan State Police were found to be using a handheld forensic device capable of extracting the entire contents of a smartphone in under two minutes — including deleted data — during routine traffic stops, raising serious Fourth Amendment concerns about...
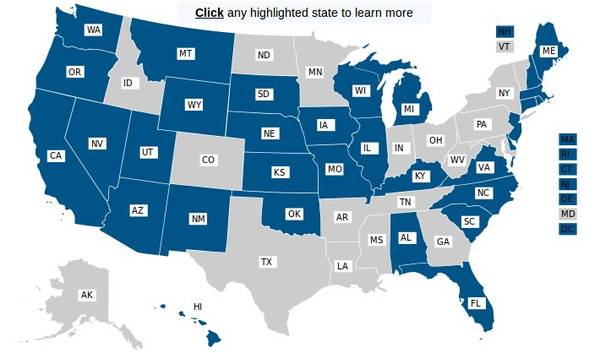
May 9, 2012 | Abuses of Power
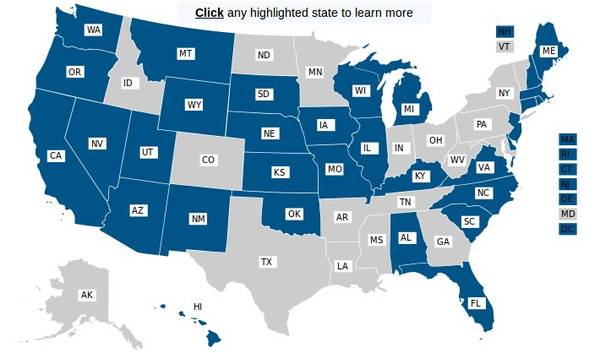
ACLU Investigation Reveals Widespread Warrantless Phone Tracking ACLU affiliates across the United States submitted public records requests to local law enforcement agencies seeking information about cell phone tracking practices. The resulting data painted a...

May 8, 2012 | WAR: By Design
The rapid expansion of America’s unmanned aerial warfare program represents one of the most consequential shifts in modern military strategy. What began as an experimental capability in the early 2000s has grown into the centerpiece of U.S. counterterrorism...

May 8, 2012 | Activism, Government Agenda, Video
In his first television interview since he resigned from the National Security Agency over its domestic surveillance program, William Binney discusses the NSA’s massive power to spy on Americans and why the FBI raided his home after he became a whistleblower. Binney...

May 4, 2012 | Abuses of Power, News
First American Arrested Using Predator Drone Surveillance The small town of Lakota, North Dakota, became an unexpected battleground over domestic drone use in 2012 when one of its residents became the first known American citizen to be arrested with the assistance of...

Apr 28, 2012 | Abuses of Power
The FBI’s ambitions to monitor social media in real time raise fundamental questions about the balance between national security and individual privacy. In early 2012, the bureau began soliciting the technology industry for help building an open-source...

Apr 28, 2012 | Activism, Video
Jacob Appelbaum: WikiLeaks Volunteer Subjected to Persistent Government Surveillance Jacob Appelbaum, a computer security researcher and volunteer with the whistleblowing website WikiLeaks, became one of the most visible examples of government surveillance targeting...

Apr 27, 2012 | Abuses of Power, News
What Was CISPA and Why Did It Matter? The Cyber Intelligence Sharing and Protection Act (H.R. 3523) emerged in late 2011 as a proposed amendment to the National Security Act of 1947. Introduced by Representatives Mike Rogers (D-MI) and C.A. “Dutch”...

Apr 26, 2012 | Abuses of Power
Obama Administration Sought to Shield NSA Surveillance Law From Court Review In 2012, the Obama administration asked the Supreme Court to dismiss a legal challenge to one of the most expansive surveillance statutes in American history — the FISA Amendments Act of...
Apr 26, 2012 | Abuses of Power, News
CISPA: The Cyber Intelligence Sharing and Protection Act Explained In April 2012, the Cyber Intelligence Sharing and Protection Act (CISPA), formally designated H.R. 3523, advanced through the U.S. Congress amid fierce debate over digital privacy and national...

Apr 26, 2012 | WAR: By Design
Pentagon Pushes for Military Operatives Under Commercial Cover The Pentagon submitted a formal proposal to Congress seeking expanded legal authority that would allow U.S. military personnel to operate overseas under the guise of civilian business activities. The...

Apr 25, 2012 | Black Technology
Sending Digital Keys Through the Human Body AT&T Labs computer scientist Brian Amento demonstrated a prototype system that turns a smartphone into a biometric door key. The mechanism works by transmitting inaudible vibrations from a phone, through the...

Apr 25, 2012 | Government Agenda, Leaks
The FBI and Department of Justice produced a series of 25 flyers under the “Communities Against Terrorism” initiative, designed to be distributed to businesses across a wide range of industries. These documents instructed employees and business owners on...

Apr 24, 2012 | Black Technology, Government Agenda
The NSA’s Massive Expansion After 9/11 In a period of extraordinary growth, the National Security Agency embarked on a construction spree that reshaped the American intelligence landscape. NSA Director General Keith Alexander traveled the country inaugurating...

Apr 24, 2012 | Black Technology
What Data Mining Actually Is and Why It Matters Data mining is the process of using automated algorithms to discover meaningful patterns, relationships, and anomalies within massive datasets. It sits at the intersection of statistics, computer science, and machine...