
Facebook is Likely Just the DARPA LifeLog Project Re-Named
Was it a mere coincidence that on the very same day that Facebook launched – February 4, 2004 – a Pentagon civilian spy project called LifeLog shut down?
5G Technology and Health: What Independent Research Reveals
5G is the term used to describe the next-generation of mobile networks beyond the 4G LTE mobile networks commonly used today. 5G is intended to be the technology that allows the Internet of Things (IOT) to exist and tie all internet connected devices together.

Impero School Monitoring Software Exposed: Critical Security Flaw Puts Student Data at Risk
Major Security Flaw Discovered in School Monitoring Software Used by Thousands of Students Impero Education Pro, one of the most widely deployed student monitoring and internet restriction tools in the United Kingdom, was found to contain a critical security...
Mysterious Shadow Hackers: The Equation Group
An unnamed scientific researcher walks out to her mailbox, shuffles through some bills and advertisements, and pulls out an envelope containing a CD of pictures from a recent scientific conference the researcher had attended in Houston. Excited – though maybe a bit...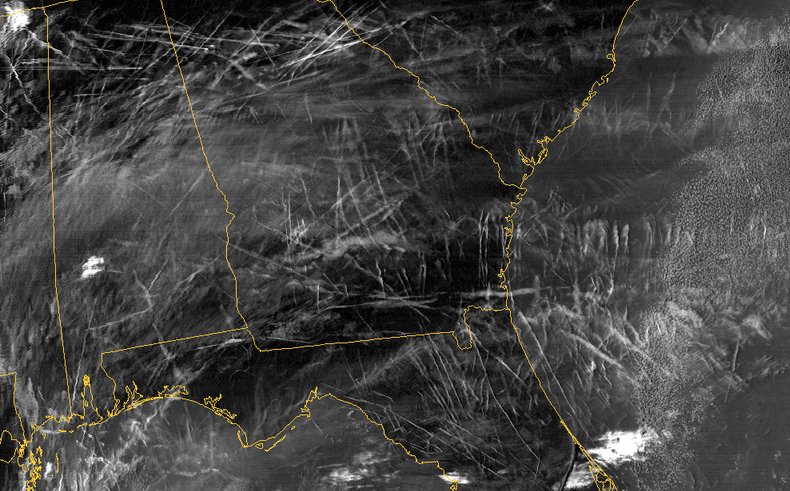
The History of Weather Modification: From Cloud Seeding to Electromagnetic Atmospheric Control
The Historical Development of Weather Modification Technology The idea of controlling weather is as old as civilization itself, but the systematic scientific pursuit of atmospheric modification began in earnest during the mid-twentieth century. What started with...
Home Hacks and Smart Grids: Data Theft Made Even Simpler
There is often times a trade-off between security and convenience. With Home Hacks the more easily you can access your personal data, the easier someone else can too, making anything that you put online a potential target for hackers. A growing source of concern for...
Deep Underground Military Bases: What We Know About Americas Hidden Bunkers
Underground Bases are Key to the Deep State and New World Order’s Ability to Stay Hidden, Permanently If-Needed Within a Vast Network of Inter-Connected (by High Speed Vacuum Sealed Tubes). Secret Programs by Every Letter Agency you can Imagine are and Have used Deep Underground Military Bases aka (DUMBs).

Mehran Tavakoli Keshe – Science, Free Energy
Mehran Tavakoli Keshe is an Iranian-born (in 1958) nuclear engineer known for his research on plasma reactors and interests in free energy applications and for his claim that he pioneered a space technology that was, according to some, used by Iran and resulted in the...
Coral Castle
Coral Castle Coral Castle is a stone structure created by the Latvian-American eccentric and mysterious Edward Leedskalnin north of the city of Homestead, Florida in Miami-Dade County at the intersection of South Dixie Highway and SW 157th Avenue.Coral Castle is a...
Voice Biometrics: How Your Speech Is Being Collected and Used to Track You
Voice biometrics technology, which converts the unique characteristics of a person’s speech into a digital fingerprint, has quietly expanded into a mass identification system used by both corporations and governments worldwide. An estimated 65 million...
Extraterrestrial UFOs are real : Ben Rich Lockheed Skunk Works CEO Admits
http://youtu.be/N7ahst8TMww Ben Rich, the “Father of the Stealth Fighter-Bomber” and former head of Lockheed Skunk Works,had once let out information about Extraterrestrial UFO Visitors Are Real. He states “we’ve” been to the stars”...
NSA Shared American Data With Israel to Surveil Palestinians
Unit 8200 Veterans Break Their Silence In September 2014, forty-three former members of Israel’s highly classified military intelligence division known as Unit 8200 took the extraordinary step of publicly refusing further service. In a jointly signed letter sent...
Court Documents Reveal Government Threatened Yahoo With 250K Daily Fines Over PRISM
Government Threatened Yahoo With Daily Fines Over PRISM Compliance In September 2014, approximately 1,500 pages of previously classified court documents revealed how the United States government coerced Yahoo into participating in the NSA’s PRISM surveillance...
Hack Back: A DIY Guide for Those Without the Patience to Wait for Whistleblowers
–[ 1 ]– Introduction I’m not writing this to brag about what an 31337 h4x0r I am and what m4d sk1llz it took to 0wn Gamma. I’m writing this to demystify hacking, to show how simple it is, and to hopefully inform and inspire you to go out...
NSA Codewords and Program Names: A Comprehensive Reference Guide
Understanding NSA Naming Conventions The National Security Agency and related U.S. intelligence organizations use a structured system of nicknames and codewords to identify their surveillance programs, tools, databases, operations, and targets. These designations...
Science Faction?
In a somewhat disturbing case of life imitating art, it seems that real world turmoil is catching up with classic science fiction projections of a dystopian future as envisioned by writers like George Orwell and Ray Bradbury — a world where the general populace...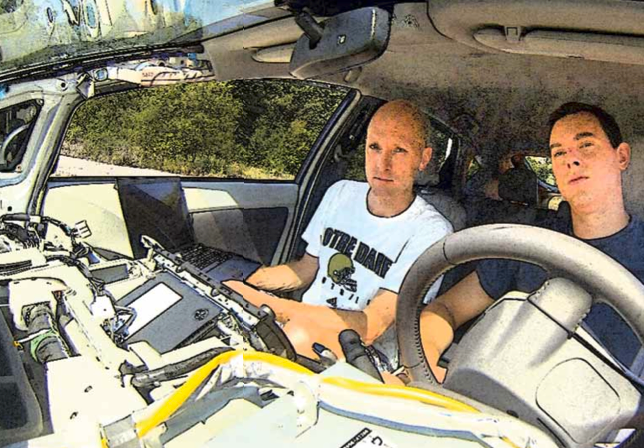
DARPA Hackers Show How Cars Can Be Remotely Controlled
Hackers Chris Valasek and Charlie Miller have demonstrated from the backseat of a Toyota Prius that all you need is a Macbook and a USB cable in order to hack into a computer-controlled car. Valasek is the director of security intelligence for IOActive and Miller is a...
Americas Most Secret Structures
http://youtu.be/HT-pJboZjxo Explore the world of secret structures- government labs, experiments gone wrong, anything is possible with Deep Underground Military Bases.
FOIA Records Reveal Extensive Military Drone Flights Over US Soil
FOIA Records Expose Domestic Military Drone Operations The Electronic Frontier Foundation (EFF) obtained and published several thousand pages of drone license records following a Freedom of Information Act lawsuit against the Federal Aviation Administration (FAA). The...
Audio Surveillance on Public Buses: The Quiet Expansion of Transit Monitoring
Transit authorities across the United States have been quietly equipping public buses with microphone-enabled surveillance systems capable of recording passenger conversations. Documents obtained by journalists revealed that cities including San Francisco, Baltimore,...
How Biometric Voiceprinting Helped Uncover a European Terror Plot
Voice Identification Technology Used in European Terror Investigation Intelligence agencies deployed biometric voiceprinting technology to identify and apprehend suspects linked to an alleged terror plot targeting multiple European countries. The British Government...Stingray Surveillance: How IMSI Catchers Threaten Cell Phone Privacy
What Are Stingray Cell Phone Surveillance Devices? Among the most invasive surveillance tools deployed by law enforcement agencies in the United States, few remain as poorly understood by the general public as the Stingray. Formally known as an International Mobile...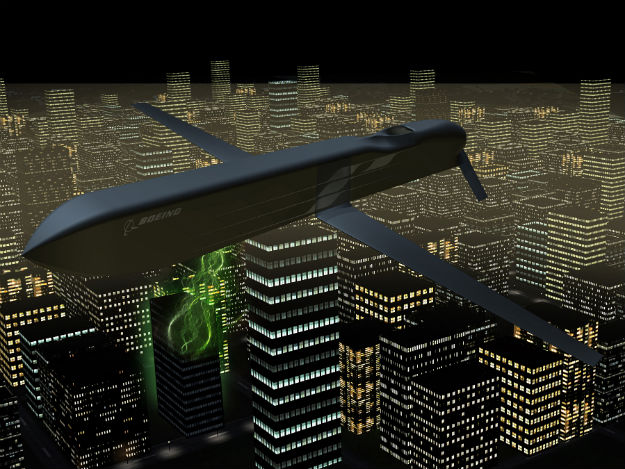
Boeing CHAMP Missile Disables Electronics With Directed Microwave Energy
The CHAMP Program: A Missile That Disables Electronics Without Explosions In October 2012, Boeing and the United States Air Force successfully tested one of the most unusual weapons in modern military development — a missile designed not to destroy targets through...
